The Top Internet of Things (IoT) Authentication Methods and Options
CTOvision
OCTOBER 12, 2020
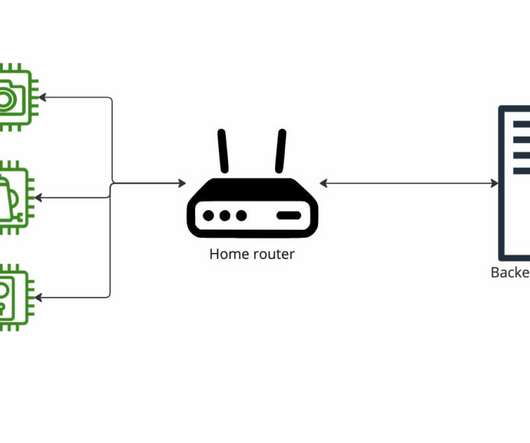
Read Ellen Boehm list top Internet of Things authentication methods and options on Security Boulevard: IoT authentication is a model for building trust in the identity of IoT machines and devices […].














































Let's personalize your content