Zero Trust: Understanding the US government’s requirements for enhanced cybersecurity
CIO
SEPTEMBER 26, 2023
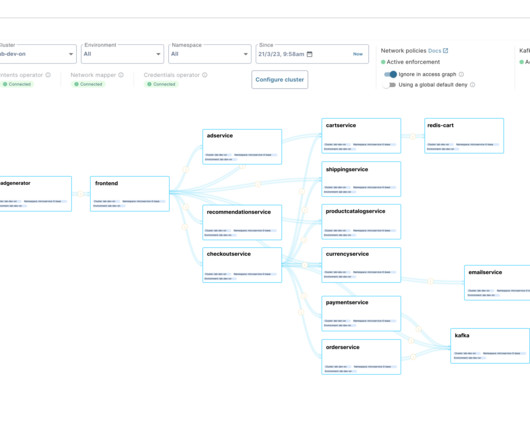
The concept of Zero Trust has gained significant traction in recent years, as organizations look to enhance their cybersecurity defenses and safeguard their digital assets. Zero Trust is a cybersecurity approach that requires organizations to assume that all network traffic, both internal and external, is untrusted until proven otherwise.

















































Let's personalize your content