How to minimize remote access cyber security threats in 2024
CIO
JANUARY 22, 2024
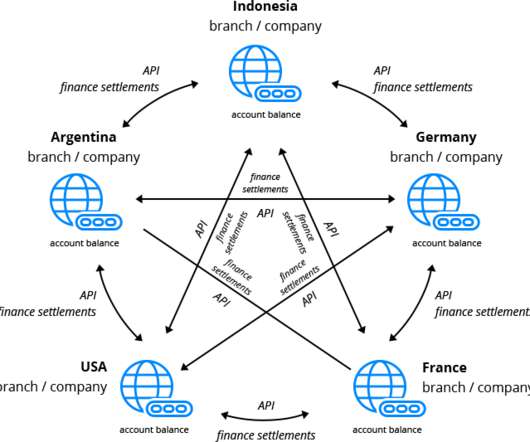
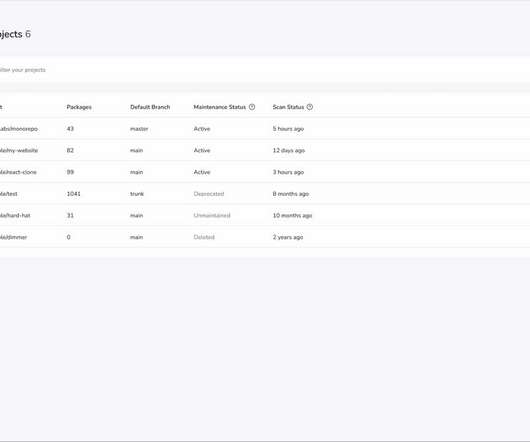
The key types of exposures, in order of prevalence, include web framework takeover, remote access services, IT and networking infrastructure, file sharing, and database exposures and vulnerabilities. Implement strong authentication methods for key internet-facing systems, such as multi-factor authentication.















































Let's personalize your content