Domain-driven data architecture
Martin Fowler
MAY 14, 2019
Zhamak explains the first part of the data mesh concept - using the ideas behind Domain-Driven Design to structure the data platform. more….

Martin Fowler
MAY 14, 2019
Zhamak explains the first part of the data mesh concept - using the ideas behind Domain-Driven Design to structure the data platform. more….

OverOps
MAY 14, 2019
As more and more companies pivot to providing software as a service, end users have come to expect that ‘service’ to always be available, fast, responsive, error-free, and to be continuously updated with new features. Containerized microservices enable developers and DevOps engineers to meet these demands. Microservices are simple to develop, test, deploy, and scale, but they’re not without their own challenges.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.

The Parallax
MAY 14, 2019
MOUNTAIN VIEW, Calif.—Google just made it much, much easier for Android device owners to protect themselves with one of the safest extra security layers available to consumers. If you have a phone or tablet running Android 7.0 or later, you are a few steps away from turning it into a two-factor authentication key , the company announced at its annual I/O developer conference here on May 7.

CTOvision
MAY 14, 2019
Read why Naga Rayapati says that artificial intelligence needs data diversity on Forbes : Artificial intelligence (AI) algorithms are generally hungry for data, a trend which is accelerating. A new breed of AI approaches, called lifelong learning machines, are being designed to pull data continually and indefinitely. But this is already happening with other AI […].
Speaker: Aarushi Kansal, AI Leader & Author and Tony Karrer, Founder & CTO at Aggregage
Software leaders who are building applications based on Large Language Models (LLMs) often find it a challenge to achieve reliability. It’s no surprise given the non-deterministic nature of LLMs. To effectively create reliable LLM-based (often with RAG) applications, extensive testing and evaluation processes are crucial. This often ends up involving meticulous adjustments to prompts.

Change Starts Here
MAY 14, 2019
In this episode, Kristy West, founder of BraveSpace, shares how you can create a climate for change using Improv techniques. You’ll hear the tenets of Improv and how they can help people be more open to change, along with some examples of exercises you can do in the workplace. Watch on YouTube: Listen to the […].
CTO Universe brings together the best content for CTOs from the widest variety of industry thought leaders.

CTOvision
MAY 14, 2019
The Boundary of Security & Privacy Privacy is becoming an ever increasing concern in our world today. Social Networks today are now focusing on users’ privacy given the inherent security risks posed by organizations’ access to personally identifiable information. The European Union has enacted GDPR valuing privacy whereas on the opposite end of the spectrum, […].

DevOps.com
MAY 14, 2019
Despite the risk of unplanned downtime, many organizations that develop software and services push them live without adequately testing for bugs that will manifest against production traffic. This is a huge gamble: Those bugs could lead to errors that bring down the service altogether. Pushing live without sufficient testing can be detrimental to your business. […].

Toptal
MAY 14, 2019
A logo redesign without controversy is like a workout with no sweat. It's possible, but is it impactful? We scrutinize high-drama logo updates and ask why they caught fire in the public arena.

DevOps.com
MAY 14, 2019
It’s crunch time in the cybersecurity industry. For too long, many companies have remained unmoved by the increasing threat of cyberattacks, despite increased digitization of their products and services. Customer data is the new gold, and some organizations are leaving the door to their vault wide open. In saying that, secure development is complex and […].

Advertisement
Multi-tenant architecture allows software vendors to realize tremendous efficiencies by maintaining a single application stack instead of separate database instances while meeting data privacy needs. When you use a data warehouse to power your multi-tenant analytics, the proper approach is vital. Multi-tenant analytics is NOT the primary use case with traditional data warehouses, causing data security challenges.

CTOvision
MAY 14, 2019
Read Larry Dignan explain how Google is using a method known as Testing with Concept Activation Vectors to help understand what signals neural networks use for prediction and identify AI bias on ZDNet : Google CEO Sundar Pichai said the company is working to make its artificial intelligence and machine learning models more transparent as […].

Toptal
MAY 14, 2019
Many product managers will struggle to identify what makes an amazing product or service. The realities of running a successful business depend on the bottom-line financials. Product managers need to define and explain value in monetary terms to drive rapid adoption.

TechBeacon
MAY 14, 2019
Cloud computing. Containers. RESTful APIs. To IT pros, these are the sexy parts of enterprise IT. Middleware, however, has never been sexy. But it has always been essential, and as your organization moves to cloud-first IT strategies, your middleware must keep pace, and you have some decisions to make.

CTOvision
MAY 14, 2019
In this world of incredible opportunity through digitization but incredibly low unemployment one thing is for sure, your business will have a hard time finding the technology leadership it needs. But in digitization one thing is for sure: Experience Matters! You can put the experienced team of technologists at OODA on your side through our […].

Advertisement
If you’re considering migrating from DataStax Enterprise (DSE) to open source Apache Cassandra®, our comprehensive guide is tailored for architects, engineers, and IT directors. Whether you’re motivated by cost savings, avoiding vendor lock-in, or embracing the vibrant open-source community, Apache Cassandra offers robust value. Transition seamlessly to Instaclustr Managed Cassandra with our expert insights, ensuring zero downtime during migration.

DevOps.com
MAY 14, 2019
New Relic today unfurled an extension of its monitoring platform specifically designed for DevOps teams tasked with managing complex IT environments. Nadya Duke Boone, vice president of product management for New Relic, said New Relic One, available to existing customers at no additional cost, makes it possible for DevOps teams to now visualize all the […].

TechSoup
MAY 14, 2019
So much data is available to your nonprofit — through your CRM, Google Analytics, social media analytics, email analytics, and beyond. When you make a dashboard, the goal should be to deliver the right data from the right time frame to the right people so that a business decision can be made. Here are the three most effective types of nonprofit dashboards, and how to build each one on a budget.

DXC
MAY 14, 2019
The world of work is about to change dramatically. Truthfully, it already has been for some time, driven by stunning advances in digital technology and a shift in the job market toward a gig economy. But the already torrid pace of change will accelerate over the next 15 years, rendering unrecognizable many of the tools […].

CTOvision
MAY 14, 2019
Artificial intelligence (AI) holds a lot of promise when it comes to almost every facet of how businesses are run. Global spending on AI is rising with no signs of slowing down — IDC estimates that organizations will invest $35.8 billion in AI systems this year. That’s an increase of 44% from 2018. With all […].

Advertisement
Embedded analytics can help you deliver cutting-edge analytics experiences to your end-users that align with KPIs that are critical to the growth and success of your business. Read this eBook to learn how an embedded analytics platform, like Qrvey, can help PMs exceed the following KPIs: Growing revenue while improving customer retention rate Delivering rapid time to value Earning a high net-promoter score Increasing Gross Margin / Profitability Conversion rate from trial to paid Don’t just meet

Tenable
MAY 14, 2019
Microsoft has released its May 2019 Security Updates, which includes a fix for CVE-2019-0708, a critical remote code execution vulnerability affecting the Remote Desktop Service. Background. Microsoft has released its monthly security update for May. Included in this month's Patch Tuesday release is CVE-2019-0708 , a critical remote code execution vulnerability that could allow an unauthenticated remote attacker to execute remote code on a vulnerable target running Remote Desktop Protocol (RDP).

Battery Ventures
MAY 14, 2019
Portfolio Spotlight: Girish Pancha, CEO of StreamSets*. Each month, Battery highlights a different portfolio-company CEO with our “Five Questions in Five Minutes” feature, showcasing the diversity of the Battery portfolio across investment stages, sectors and geographies. What does your company do in 10 words or less? We’re modernizing data integration for fast, big, cloud data analytics.

CTOvision
MAY 14, 2019
Read Joshua P. Meltzer’s article about how artificial intelligence can be used to impact economic, trade, and social opportunities on the Brookings Institute Blog : Artificial intelligence (AI) has the potential to transform economic growth, commerce, and trade, affecting the types of jobs that are available and skills that are needed. The United States, China, […].

Confluent
MAY 14, 2019
A technology community is made up of people. Without people writing code, writing tutorials, welcoming newcomers, giving presentations, and answering questions, what we have is not a community, but just a set of Git repositories. We’re grateful that the Apache Kafka ® and Confluent communities are composed of hundreds of thousands of people all over the world who are constantly doing all of these things.
Advertisement
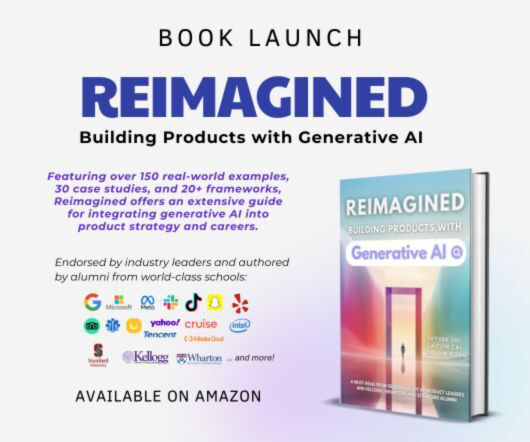
“Reimagined: Building Products with Generative AI” is an extensive guide for integrating generative AI into product strategy and careers featuring over 150 real-world examples, 30 case studies, and 20+ frameworks, and endorsed by over 20 leading AI and product executives, inventors, entrepreneurs, and researchers.

TechBeacon
MAY 14, 2019
Every organization wants to be cyber-resilient. Most teams attack the problem from the bottom up, using a horizontal software development lifecycle (SDLC) mindset such as security requirements, threat modeling, code scanners, etc. Unfortunately, while these approaches are useful, they don't scale well.

Cabot Solutions
MAY 14, 2019
Improved Application Testing through automated Appium testing and AWS Device Farm Appium testing with AWS Device Farm gives you more control over the testing environment and how apps would perform on real mobile devices Check out this blog to know more

PowerSchool
MAY 14, 2019
A father-son story spanning PowerSchool careers and campuses, from our Diversity and Inclusion Office. Nicolas Bonatto, at 11, with his dad Rick Bonatto, a PowerSchool programmer in 2003, at the Take Our Sons and Daughters to Work Day at PowerSchool. Nicolas Bonatto was 11 years old when he first walked into PowerSchool. It was Take Our Sons and Daughters to Work Day in 2003.

Aqua Security
MAY 14, 2019
For the second time, Aqua will host the KubeSec Enterprise Summit next week, together with our co-hosts AWS, Google Cloud, Microsoft Azure, and Red Hat. The event is co-located with KubeCon/CloudNativeCon in Barcelona and will take place on Monday, May 20th. Unlike other co-located events, this full day event focuses on the challenges faced by enterprises with demanding security and compliance requirements when deploying Kubernetes in production.

Advertisement
Outdated or absent analytics won’t cut it in today’s data-driven applications – not for your end users, your development team, or your business. That’s what drove the five companies in this e-book to change their approach to analytics. Download this e-book to learn about the unique problems each company faced and how they achieved huge returns beyond expectation by embedding analytics into applications.

Teradata
MAY 14, 2019
Cheryl Wiebe explains why AI for industrial use cases is a more complicated road than it appears.

DevOps.com
MAY 14, 2019
Point72 Ventures leads funding round to address performance and complexity challenges of modern data applications and cloud migration initiatives PALO ALTO, Calif.,—May 14, 2019—Unravel Data, the only data operations platform providing full-stack visibility and AI-powered recommendations to drive more reliable performance in modern data applications, today announced it has raised $35 million in an oversubscribed […].

Arista
MAY 14, 2019
I am very excited about our next-generation R3 Series routing platforms, which are setting new standards for throughput, density, power efficiency and price performance. We designed these products to address the growing bandwidth demands in cloud datacenter and public networks, supported by significant Arista EOS enhancements including route scale, telemetry and security.
Let's personalize your content