Tractable raises $60M at a $1B valuation to make damage appraisals using AI
TechCrunch
JUNE 16, 2021
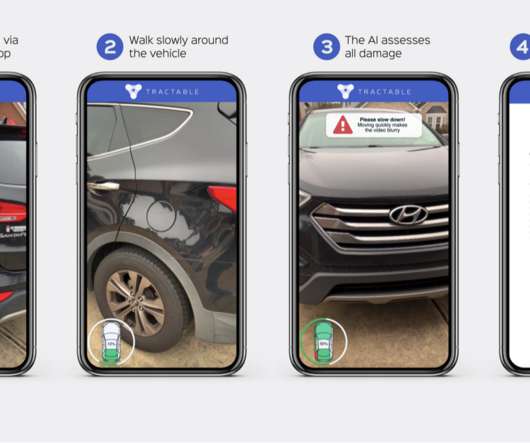
As the insurance industry adjusts to life in the 21st century (heh), an AI startup that has built computer vision tools to enable remote damage appraisals is announcing a significant round of growth funding. Tractable , which works with automotive insurance companies to let users take and submit photos of damaged cars that are then “read” to make appraisals, has raised $60 million, a Series D that values Tractable at $1 billion, the company said.






































Let's personalize your content