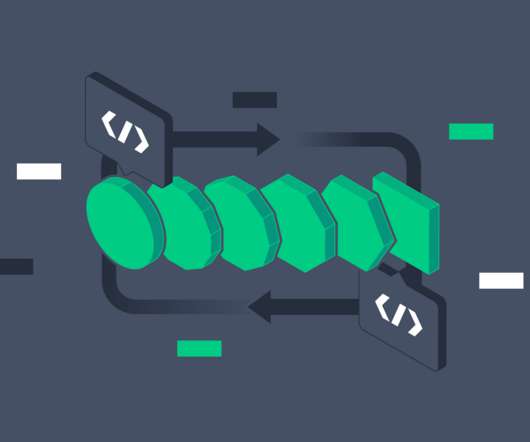
How to Achieve AWS Security in 10 Steps
DevOps.com
JULY 27, 2020
Looking to lock down your AWS cloud service? Here are the 10 steps to take for AWS security As more companies embrace the cloud, security is becoming a more significant challenge. Irrespective of size, organizations are increasingly realizing the importance of having proper cloud security practices in place. More and more companies are creating a […].

































Let's personalize your content