The 6 Core Skills of a Good Data Scientist
Dataiku
JUNE 19, 2020
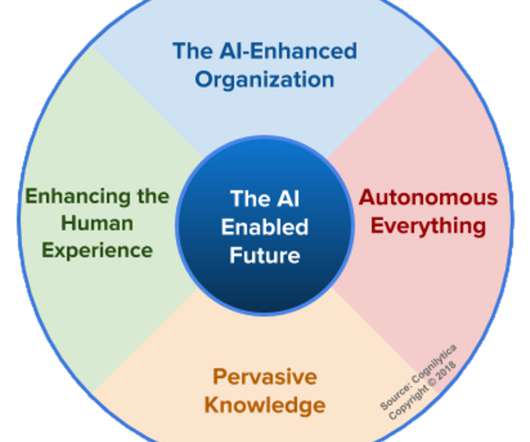
The term “ data scientist ” was coined in 2008 by two LinkedIn analysts to describe their work deriving business value from the masses of data being generated by their website. Since then, people haven't stopped wondering what a data scientist really is (even some companies looking to hire them aren't so sure). If you're seeing an intrepid data scientist to lead your company on the path to Enterprise AI, what skill sets should you be looking for?


































Let's personalize your content