Data Lake vs Data Warehouse
The Crazy Programmer
MAY 12, 2021
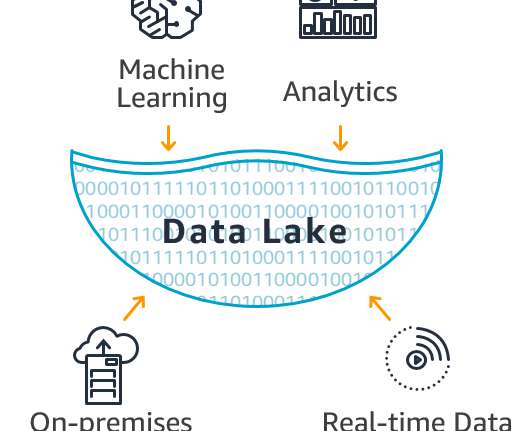
Companies everywhere are handling more data than ever and all these terabytes of data need to be stored somewhere. Should you store the data in a database, a data warehouse, or a data lake? How do you know what is best for your company? Choosing the right data storage solution will depend greatly on how the data is going to be used. While both a data lake and a data warehouse share the goal of the process data queries to facilitate analytics, their functions are different.

































Let's personalize your content