UScellular and Palo Alto Networks Join Forces to Secure 5G
Palo Alto Networks
FEBRUARY 21, 2024
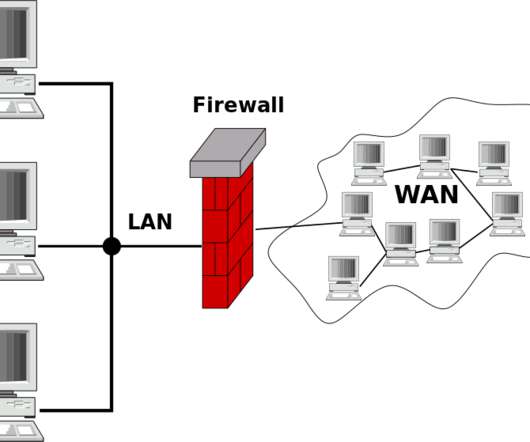
Remember when securing your network meant throwing up a firewall and calling it a day? Now, UScellular and Palo Alto Networks are teaming up once again to tackle the ever-growing security challenges of LTE, 5G and Gi-LAN networks. First, Palo Alto Networks NGFWs, specifically PA-7080 models, are ideally suited for Gi-LAN environments.





















Let's personalize your content