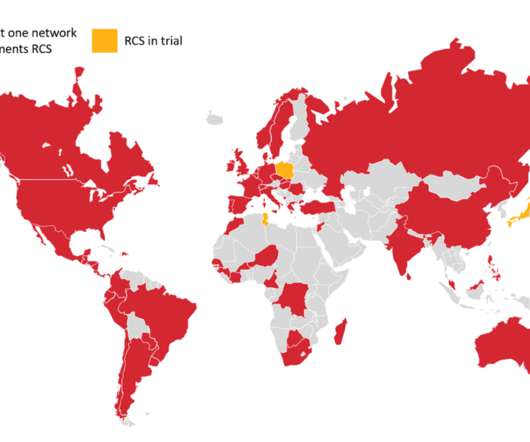
How Regulation Is Impacting 5G Security in Europe
Palo Alto Networks
DECEMBER 14, 2020
Over the past few years, I have witnessed a growing focus in Europe on telecom and 5G security. Many service providers in the region are evolving cybersecurity practices and postures, both for existing 4G networks and also for planned 5G deployments, many of which are launching now. Annex I, Section 2.2
















Let's personalize your content