Dealing with MITRE ATT&CK®’s different levels of detail
Lacework
OCTOBER 24, 2023
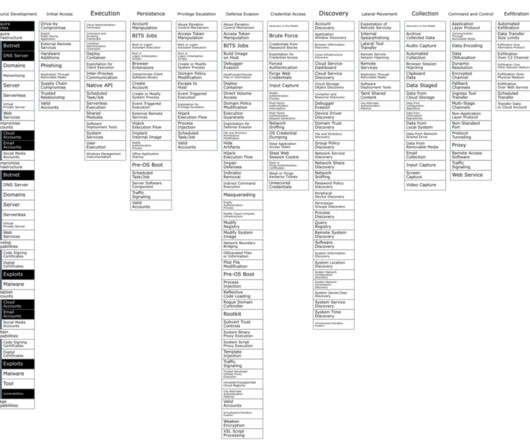
In this blog post, we attempt to answer the question: from the perspective of a Detection Engineering team, which techniques do we need to focus on and which can we safely ignore? Figure 3: Firmware modification is a data source that is not typically used in SIEM Phishing There are many techniques that are listed under multiple tactics.






















Let's personalize your content