Powering digital transformation
CIO
MARCH 26, 2024
Harness the power of endpoint management In today’s dynamic work environment, managing a diverse range of endpoint devices is crucial for communication, collaboration, and productivity.
This site uses cookies to improve your experience. By viewing our content, you are accepting the use of cookies. To help us insure we adhere to various privacy regulations, please select your country/region of residence. If you do not select a country we will assume you are from the United States. View our privacy policy and terms of use.

 products endpoint
products endpoint 
CIO
MARCH 26, 2024
Harness the power of endpoint management In today’s dynamic work environment, managing a diverse range of endpoint devices is crucial for communication, collaboration, and productivity.

CIO
MARCH 6, 2024
IT professionals now need capabilities that allow them to remotely support and secure user devices, as well as solutions that maximise their own productivity. Functionality that improves productivity Technology should be seamless and powerful. Find out more on how to maximise productivity and empower teams here. Remote Work
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.

CIO
MARCH 26, 2024
Automated workflows and cloud document management systems eliminate delays and administrative hurdles, streamlining processes, and optimizing productivity. Endpoint management Endpoint management provides organizations with the ability to efficiently manage, update, and secure endpoint devices while optimizing the employee experience.

CIO
MARCH 6, 2024
Harness the power of endpoint management In today’s dynamic work environment, managing a diverse range of endpoint devices is crucial for communication, collaboration, and productivity.

CIO
MARCH 6, 2024
Over the past few years, more businesses have adopted digital workspaces to enable a seamless and productive hybrid work experience. Endpoint Protection, Remote Work This is an IT reality that is unlikely to change. No matter where they’re logging in from.

CIO
MARCH 26, 2024
Automated security policies HP Adaptive Endpoint Management helps automate security updates from the cloud. Adaptive Endpoint Management enabled HP to rationalize its device management practices by streamlining policy management and using a corporate-ready device image. Click here to read the full case study. Remote Work, Security

CIO
MARCH 6, 2024
Rapid adoption of remote work during the pandemic proved that organizations could be successful and employees productive and happy while working outside of the office. The workplace has fundamentally changed. But the long-term reality for many companies is that employees aren’t working exclusively in offices or at home.

CIO
MARCH 26, 2024
Securing endpoints for remote workers The majority of remote workers tend to use their own personal devices to do their work, either on their own initiative or through a Bring-Your-Own-Device (BYOD) policy. The workforce is no longer bound to the traditional workplace, requiring you to transform your organization’s ways of working.

CIO
MARCH 26, 2024
Organizations across all industries can leverage digital workspaces to implement hybrid work models that (1) provide employees with a superior user experience, (2) meet security, productivity, collaboration, and employee satisfaction goals for the business, and (3) are manageable for IT. What is a digital workspace? Remote Work

TechCrunch
APRIL 26, 2023
It bundles several different products that all revolve around cybersecurity risks with a software-as-a-service approach. Companies we talk with tell us: ‘We have an insurance broker, an accountant, why would we have multiple cybersecurity products?’” Third, Bastion scans and protects endpoints, such as employee laptops. “We

CIO
MARCH 26, 2024
Workers around the world are broadly positive about the idea of returning to the office, at least part-time, but CIOs should know that many are also skeptical about the suitability of in-office technology to sustain productivity. But even where meeting rooms did exist, they often did little for productivity.

CIO
OCTOBER 12, 2022
Microsoft is reshuffling its branding around endpoint management: Intune, previously a component of its enterprise mobility management offering, is now the umbrella brand for its whole range of endpoint management products such as Configuration Manager — with the promise of more to come. Innovation
CIO
JULY 27, 2022
Later he joined SAP Labs in the US where he was immersed in product management for cloud technology. We embrace proven technologies like the Microsoft platform for endpoint management servers, active directory, email and endpoint protection. Since 2013 he’s been overseeing the Dangote Group’s IT operations across Africa. .

CIO
OCTOBER 10, 2023
A technology that can greatly improve the efficiency of organizations – allowing them to be significantly more productive with the same number of human resources. About Alex Au Yeung Broadcom Software Alex Au Yeung is the Chief Product Officer of the Symantec Enterprise Division at Broadcom. Generative AI

CIO
OCTOBER 4, 2023
Reasons for this limitation include data sovereignty and residency requirements, the need to support ultra-low latency workloads, and concerns about losing control over mission-critical use cases, such as production assembly lines or retail point-of-sale systems. Edge Computing

CIO
OCTOBER 16, 2023
Specifically, we’re looking at whether AI will make employees more productive or satisfied in their jobs. AI can unlock developer productivity by allowing teams to bridge the knowledge and change context to gain new information and solve issues faster. AI app accelerators are ushering in a new era of AI-driven intelligent assistance.
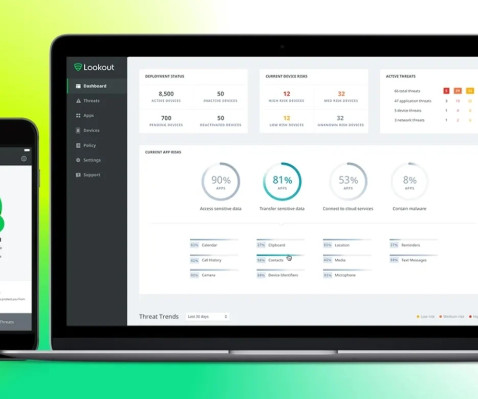
TechCrunch
APRIL 26, 2023
Lookout says that with this transaction, which it expects to conclude within the next two months, its business will “now evolve into a pure-play enterprise company,” focusing on mobile endpoint security and cloud security. ” For F-Secure, the deal gives it a stronger foothold in the U.S.

CIO
AUGUST 23, 2023
Today’s management and infrastructure are designed to populate a data lake with valuable information that helps accurately determine the type of endpoint clients that are on your network. We’ve created a short podcast where we discuss this topic further so that you can hear directly from Ziad Hadi, Product Line Manager for Client Insights.
AWS Machine Learning - AI
APRIL 8, 2024
It is not recommended that you use this credential in a production environment. Choose Deploy again to create the endpoint. The endpoint will take approximately 5–10 minutes to be in service. You can locate the endpoint name in either the output of the SDK or in the deployment details in the SageMaker JumpStart UI.
Xebia
FEBRUARY 4, 2024
server { listen ${load_balancer_ip}:80; resolver 169.254.169.254; location / { # Note: Please include additional security for a production deployment. Exposing all reachable HTTP endpoints is probably not intended. Exposing all reachable HTTPS endpoints is probably not intended. NOTE: Order of interfaces matter.

CIO
FEBRUARY 7, 2024
We’ve seen an ongoing iteration of experimentation with a number of promising pilots in production,” he says. Samsara employees are applying these general-purpose assistants to a variety of use cases, like writing documentation and job descriptions, debugging code, or writing API endpoints.

TechCrunch
APRIL 20, 2023
“We view our product as unique in that we have no direct competitors, and in fact want to improve other security tools in use by our customers,” Miller, who serves as CEO, said. That’s why we have focused on building a product with resilience in mind.” Halcyon’s approach sounds like a clever way to combat this.

CIO
OCTOBER 16, 2023
When considering a new terminal emulation solution, organizations tend to be concerned about the conversion impact — the duration of the migration, the end-to-end skills needed, the productivity outcomes that can be expected, and the impact of a rip and replace on day-to-day operations and employee morale. Because TLS 1.3

TechCrunch
APRIL 19, 2022
Not much attention has been paid to the type of autonomy Steer Tech, a Maryland-based AV startup, has been pursuing — something the company’s founder and CEO Anuja Sonalker calls “endpoint autonomy.” Steer wants to bring this ecosystem to the endpoint of the logistics supply chain. My goal here is to build a product.
TechCrunch
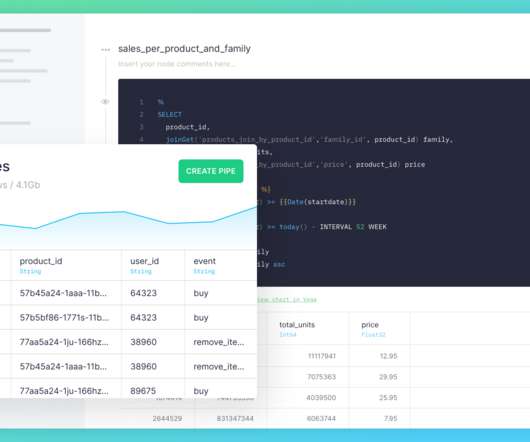
JULY 5, 2021
Meet Tinybird , a new startup that helps developers build data products at scale without having to worry about infrastructure, query time and all those annoying issues that come up once you deal with huge data sets. The company ingests data at scale, lets you transform it using SQL and then exposes that data through API endpoints.

Ivanti
FEBRUARY 13, 2024
Improving DEX delivers benefits for IT efficiency, employee productivity and retention, unified endpoint management (UEM) and even cybersecurity. It comes down to this: to improve digital experiences being delivered via digital endpoints, you need to know what and where your endpoints are. Where are they?

TechCrunch
MAY 9, 2023
SquareX wants to serve as an alternative to current cybersecurity products by being tailor-made for browser-based cloud SaaS tools. As a result, Ramachandran realized that many security products are actually counterproductive because they make people less likely to use them. Instead, it uses its disposable browsers.

TechCrunch
DECEMBER 14, 2020
Christy Wyatt is Chief Executive Officer and a member of the board of directors at Absolute , a leader in endpoint resilience solutions and the industry’s only undeletable defense platform embedded in over a half-billion devices. Christy Wyatt. Contributor. Share on Twitter.

Ivanti
FEBRUARY 9, 2024
The dangers of bad DEX Knowledge workers who use digital technology to perform job tasks face an endpoint management challenge an average of 919 times per year, or approximately 3.67 Some of those issues are minor but so repetitive they become excessively time-consuming for IT staff, driving up IT costs and reducing productivity.

CIO
SEPTEMBER 21, 2023
From a general IT perspective, I am most excited about the emerging use of AI and how it may be leveraged to automate certain tasks, increase productivity, and improve service to our guests. How do you defend the casino against attacks such as breaches, ransomware, or insider threats? It’s already pretty good at helping with math homework.

Kaseya
OCTOBER 25, 2023
Any tool that can automate daily tasks and free technicians from the curse of monotony can exponentially boost their productivity and result in massive IT improvements for the organization. Conquer your fears with Kaseya VSA As the number of endpoints continue to rise, the resources available to manage them are dwindling. But fear not!

CIO
SEPTEMBER 2, 2022
Addressing this security challenge requires a renewed focus on endpoint security. Intel provides new security features thought vPro which are designed to renew that endpoint security layer.

CIO
SEPTEMBER 2, 2022
Addressing this security challenge requires a renewed focus on endpoint security. Intel provides new security features thought vPro which are designed to renew that endpoint security layer.

Ivanti
NOVEMBER 9, 2023
This is compelling organizations to embrace device and asset monitoring under a “single pane of glass,” meaning via a unified, “single console” view of their entire network to enable unified endpoint management (UEM). You’ll rest easy knowing that all endpoints have been discovered, properly managed and secured.
AWS Machine Learning - AI
JANUARY 9, 2024
When it comes to deploying models on SageMaker endpoints, you can containerize the models using specialized AWS Deep Learning Container (DLC) images available for popular open source libraries. Now that you have defined the model and model config, you can create the SageMaker endpoint.

TechCrunch
MAY 7, 2021
Jason Meller is the founder and CEO of Kolide , an endpoint security solution for teams that value productivity, transparency and employee happiness. To make matters worse, we lacked the confidence in our product and strategy, so we developed our solution with hesitancy, underspending in critical areas. Jason Meller. We stalled.

CIO
SEPTEMBER 7, 2023
Production lines, networks, call centers: every aspect of your organization is being revolutionized in different ways by technology such as AI, automation, edge computing and the many flavors of cloud. You can use AI and machine learning across security, networking and user experience management, all in the same data lake.

InnovationM
APRIL 25, 2024
API Setup: Set up an API endpoint within your RunPod environment to interface with the deployed LLM model. You can use frameworks like Flask or FastAPI to create the API endpoints. Embrace RunPod today and embark on a journey towards unparalleled performance and productivity in your computational endeavors.

TechCrunch
MARCH 23, 2022
As an investor and a recent product manager, I have encountered many companies that failed and some that succeeded at their product-led growth (PLG) efforts. One pervasive approach to embarking on a PLG journey is to create a sign-up page and make the whole product available for self-serve consumption. Vidya Raman. Contributor.

Honeycomb
MARCH 14, 2024
Questions you will be able to answer: Which API endpoints are returning slowly and what is normal? Which API endpoints get the most errors? Questions you won’t be able to answer: Are endpoints slower for baskets with more items? Which third parties are responding slowly? What are the slowest database calls?

CTOvision
NOVEMBER 4, 2020
Attivo Networks announced innovative enhancements to its ThreatPath solution, part of the modular ThreatDefend Endpoint Detection Net (EDN) family of products. ThreatPath, which continuously observes and shows credential exposures, now also […].

Palo Alto Networks
NOVEMBER 13, 2023
We believe that these problems can be boiled down into three fundamental areas: Siloed Tools and Data – Today’s SOCs are built on a variety of disparate tools that address specific security functions (endpoint security, automation, incident and event management, etc.). All of these tools have different consoles and store data separately.

DevOps.com
NOVEMBER 2, 2022
Tanium this week added the ability to detect libraries and software packages with known vulnerabilities within a software bill of materials (SBOM) manifest that can then be used to automate remediation of endpoints running vulnerable code. The post Tanium Uses SBOMs to Automate Vulnerability Remediation appeared first on DevOps.com.

Kaseya
MARCH 18, 2020
While switching to a remote workforce is a welcome move, it brings with it a slew of challenges, the biggest being the need to ensure business continuity with minimal loss of productivity. Use an endpoint management solution for remote monitoring and management. Automate many routine IT management tasks.
Expert insights. Personalized for you.
Are you sure you want to cancel your subscriptions?

Let's personalize your content