RSA 2022: Progress in Combating Ransomware: Honest Insights from the Ransomware Task Force
Symantec
JUNE 8, 2022
government has made some progress against ransomware, challenges to disrupt these activities remain While the U.S.
This site uses cookies to improve your experience. By viewing our content, you are accepting the use of cookies. To help us insure we adhere to various privacy regulations, please select your country/region of residence. If you do not select a country we will assume you are from the United States. View our privacy policy and terms of use.

 ransomware-task-force
ransomware-task-force 
Symantec
JUNE 8, 2022
government has made some progress against ransomware, challenges to disrupt these activities remain While the U.S.

CIO
NOVEMBER 7, 2023
Ransomware Attacks: Ransomware attacks pose a substantial threat to critical infrastructure. In addition, botnets can be used for data theft, spam distribution, and ransomware dissemination. Cyber attacks often aim to disrupt operations, and a power outage can serve as a force multiplier for these disruptions.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.

Palo Alto Networks
SEPTEMBER 28, 2023
Ransomware attacks have evolved over the years from a threat primarily targeting individuals with modest ransom demands, to a sophisticated form of cybercrime that now jeopardizes large companies, government agencies and critical infrastructure. Sam Rubin's testimony on ransomware attacks. We call this multi-extortion.

Tenable
SEPTEMBER 15, 2023
Tasked with securing your org’s new AI systems? 1 - Google: The ins and outs of securing AI systems As businesses adopt artificial intelligence (AI) and cybersecurity teams get tasked with protecting these complex new systems, a fundamental question looms: When defending AI systems, what changes and what stays the same? And much more!
CIO
OCTOBER 5, 2023
This, in turn, is forcing businesses to rethink the way they operate, engage, and go to market. Consider how the time to execute ransomware attacks has been reduced by 94 percent. This significantly reduces administrative tasks for nurses, enabling them to focus more time on life-saving activities.

Tenable
MARCH 1, 2024
In their paper “ Considerations for Evaluating Large Language Models for Cybersecurity Tasks, ” the authors state that current assessment methods fall short, because they focus on evaluating LLMs’ factual knowledge by, for example, having them take a cybersecurity certification exam.

Palo Alto Networks
OCTOBER 29, 2021
Australia's Ransomware Action Plan. On October 13, the Australian Government released its Ransomware Action Plan , which identifies initiatives to address the rise of ransomware across key themes of prepare and prevent, respond and recover, as well as disrupt and deter. Ransomware on the Rise.

Tenable
NOVEMBER 4, 2022
Get the latest on salary trends for CISOs and cybersecurity pros; CISA’s call for adopting phishing-resistant MFA; the White House’s ransomware summit; and more! You can also watch this CISA video: 4 – White House hosts global anti-ransomware summit. 31, 2022: Ransomware, which Cameron called “the most acute threat” to U.K.
Palo Alto Networks
MARCH 23, 2023
Today’s ransomware gangs are constantly evolving their tactics to pressure organizations to pay ransoms. Based on extensive research from the Unit 42 threat intelligence and response teams, the 2023 Unit 42 Ransomware and Extortion Report exposes how active ransomware groups are increasing the pressure on targeted organizations.

Tenable
DECEMBER 2, 2020
government’s ICT Supply Chain Risk Management Task Force includes guidance on vulnerability management, mitigation and prioritization as key to understanding operational risk. As chair of the IT Sector Coordinating Council , I’m especially proud that we are one of three chartering organizations of the ICT SCRM Task Force.

Tenable
MARCH 24, 2022
Private messages between Conti members uncover invaluable information about how the infamous ransomware group hijacks victims’ systems. The ContiLeaks began on February 27 – the work of an alleged member of the Conti ransomware group. Ransomware groups like Conti use a variety of tactics to breach the networks of prospective targets.
The Crazy Programmer
MARCH 29, 2022
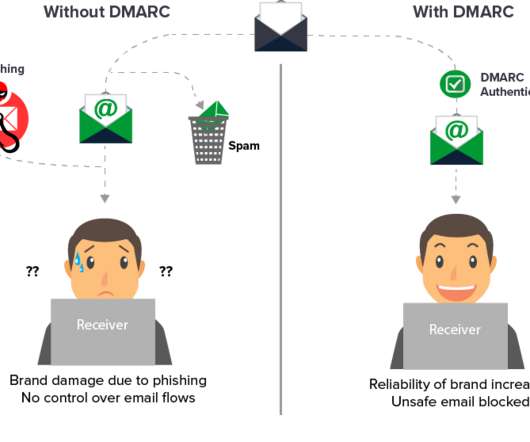
DMARC is now in the process of being accepted as an open standard by the Internet Engineering Task Force (IETF). Scams and misuse of a well-known brand Ransomware and Malware assaults Employees are at risk of falling victim to spear phishing and CEO fraud. All major Internet service providers (ISPs) presently support DMARC.

Ivanti
SEPTEMBER 21, 2023
According to a recent report, 43% of hospitals have been victims of ransomware in the past year. Cyberattacks on hospitals can range from data breaches to ransomware attacks. In 2020, several hospitals around the world were hit by ransomware attacks that led to critical systems being locked down or disrupted entirely.
Ivanti
AUGUST 3, 2021
Ransomware is a strain of malware that blocks users (or a company) from accessing their personal data or apps on infected iOS, iPadOS, and Android mobile devices, macOS laptops, Windows personal computers and servers, and Linux servers. There are 4 main types of ransomware. The other is Ransomware-as-a-Service (RaaS).

Haft of the Spear
JUNE 20, 2021
The scourge of ransomware is the inevitable result of decades of schizophrenia about our relationship with information technology and security. Clarity, creativity, and will are required if we are to have any hope of a future where ransomware is an annoyance and not a plague. Don’t hold your breath. Über Alles.

Tenable
SEPTEMBER 8, 2023
2 - OT security teams get new adversary-emulation tool Are you tasked with securing your organization’s operational technology (OT) systems? Security Spotlight - Episode 1: The Ransomware Ecosystem Tenable.ot Security Spotlight - Episode 2: The Business Risk From a Ransomware Attack on OT Systems Tenable.ot

Palo Alto Networks
JANUARY 25, 2022
Properly resourcing the Cybersecurity and Infrastructure Security Agency (CISA) will act as a force multiplier to ensure that investment in cybersecurity resilience is met with technical assistance and services to help organizations with capacity building. That focus, coupled with dedicated funding, can meaningfully move the needle.

Palo Alto Networks
SEPTEMBER 6, 2023
Beyond ensuring the site was up and running, my task was to safeguard it from emerging cyberthreats. CISOs must implement intelligent systems to ensure only critical tasks are seen by analysts and everything else is automated. Websites were becoming digital storefronts, and the role of a webmaster was pivotal.
O'Reilly Media - Ideas
MAY 2, 2023
AutoGPT means the creation of ChatGPT agents that execute tasks for the user without intervention. These tasks typically include additional ChatGPT requests, with automatically generated prompts. This could be a big step forward in GPT-4’s accuracy, at least for programming tasks. What’s beyond ChatGPT?
O'Reilly Media - Ideas
JULY 5, 2022
It’s sadly unsurprising that a robot incorporating a widely-used neural network (OpenAI CLIP) learns racist and sexist biases , and that these biases affect its performance on tasks. In the first quarter of 2022, the number of known ransomware attacks was down 40% , largely due to the disappearance of the Conti ransomware group.

Xebia
JANUARY 19, 2023
Their work would be devoted to cluster administration and maintenance, managing overhead, and writing pipeline and transformation jobs, among other tasks. Architects should avoid decisions that will hamper the productivity of engineers working on domain-specific problems by forcing them into one-size-fits-all technology solutions.

O'Reilly Media - Ideas
NOVEMBER 2, 2021
It’s also important that machine learning seems to have taken a step (pun somewhat intended) forward, with robots that teach themselves to walk by trial and error, and with robots that learn how to assemble themselves to perform specific tasks. SRE is intentionally a scarce resource; teams should solve their own problems. Devices and Things.

Kaseya
JANUARY 12, 2023
For example, an attacker can exploit a vulnerability in a web application to gain access to sensitive data, cause damage and business disruption, or launch a ransomware attack. Cybercriminals can break simple username and password combinations through brute force attacks, enabling them to carry out their malicious plans.

Palo Alto Networks
MAY 14, 2021
Ransomware is one of society’s most pervasive threats, growing from a cybercrime nuisance to a critical risk to national and global security, economic stability, and public safety. Existing and emerging security technologies can play a critical role in helping address the ransomware crisis.

O'Reilly Media - Ideas
AUGUST 10, 2021
The concept behind ransomware is simple. Recently, ransomware attacks have been coupled with extortion: the malware sends valuable data (for example, a database of credit card numbers) back to the attacker, who then threatens to publish the data online if you don’t comply with the request. But what about ransomware?

Kaseya
JANUARY 12, 2023
For example, an attacker can exploit a vulnerability in a web application to gain access to sensitive data, cause damage and business disruption, or launch a ransomware attack. Cybercriminals can break simple username and password combinations through brute force attacks, enabling them to carry out their malicious plans.

The Parallax
SEPTEMBER 25, 2018
government-sponsored Health Care Industry Cybersecurity Task Force delivered more than 100 recommendations to the Department of Homeland Security to make medical technology more resistant to hackers. But in the 15 months since the report was published, only one recommendation has been adopted, according to two task force members.

Kaseya
OCTOBER 4, 2023
CEO Fred Voccola’s keynote: a year of progress and the road ahead In the opening keynote of Kaseya DattoCon 2023, CEO Fred Voccola shared the remarkable journey of the past year since Kaseya and Datto joined forces. This integration extends to the automation of various tasks and the simplification of the partner experience.

Saviynt
FEBRUARY 25, 2019
In 2018, Distributed Denial of Service (DDoS) remained a problem, as was human error that fueled several ransomware attacks. With digitization comes risk, yet companies are forced to remain viable and “see around corners” to plan for the inevitable. An IT exodus is anticipated in 2020 when 34.3%

Saviynt
FEBRUARY 25, 2019
In 2018, Distributed Denial of Service (DDoS) remained a problem, as was human error that fueled several ransomware attacks. With digitization comes risk, yet companies are forced to remain viable and “see around corners” to plan for the inevitable. An IT exodus is anticipated in 2020 when 34.3%

The Parallax
AUGUST 7, 2018
But the design, testing, delivery, and installation of security patches is no simple task—and it’s especially complicated for medical or critical-infrastructure hardware. Standardizing and publishing SBOMs could streamline tasks for people like him. Although software vendors are not currently required by U.S. government.

Kaseya
FEBRUARY 14, 2023
In 2022, 71% of companies worldwide were affected by ransomware , with 62.9% of ransomware victims paying the ransom. Network analysis and reporting: This task involves measuring data transmission efficiency using latency, jitter, packet loss and throughput metrics. Threats are not only increasing in number but also complexity.

Infinidat
MAY 23, 2023
All of these features are an inherent part of InfuzeOS™, our core operating system that is the driving force at the heart of all our storage devices - the InfiniBox® and InfiniBox™ SSA primary storage solutions, as well as the InfiniGuard® secondary storage platforms. Infinidat drives the right solutions for our enterprise customers' needs.”

Openxcell
MARCH 15, 2023
Companies are simultaneously figuring out how to complete outsourced tasks faster and cheaper. Whatever the driving force, it is certain that outsourcing is already proving to be a crucial strategy in 2023 and that this will only continue into the following years.

Palo Alto Networks
FEBRUARY 7, 2023
Every day, IBM Security X-Force works with organizations to prevent, detect, respond and recover from cyberattacks. Choosing the right security tools is critical to keeping team members focused, productive and ready to respond when ransomware, data breaches and other cyberthreats put clients at risk.

Tenable
FEBRUARY 23, 2024
Check out how cyber agencies from multiple countries hit the LockBit ransomware group. 1 - LockBit ransomware gang disrupted in multinational cyber operation LockBit, one of the world’s most destructive ransomware groups, just got dealt a powerful blow. And the White House seeks to boost ports' cybersecurity. And much more!

Kaseya
DECEMBER 15, 2023
For example, configuration management involves tracking the version of software installed on each device as well as the settings and security policies that are in force. ITSM minimizes bottlenecks and streamlines workflows so that tasks can be completed on time and efficiently.

Kaseya
OCTOBER 28, 2021
A cybercriminal can deploy a multitude of attack vectors to deliver malicious payloads, such as viruses, worms and ransomware code, into a victim’s system and sabotage their operations. Malware and Ransomware . The infection can take the form of a virus, trojan horse, worm, spyware, adware, rootkit or the infamous ransomware.

The Daily WTF
DECEMBER 14, 2021
Which means, yes, definitely ransomware attacks are happening. But getting everyone on the planet to upgrade or fix is one of those unlikely tasks. That one's at a payroll company, but there were a lot of places that were vulnerable , and the exploit was in the wild before being reported. And it's being widely exploited.
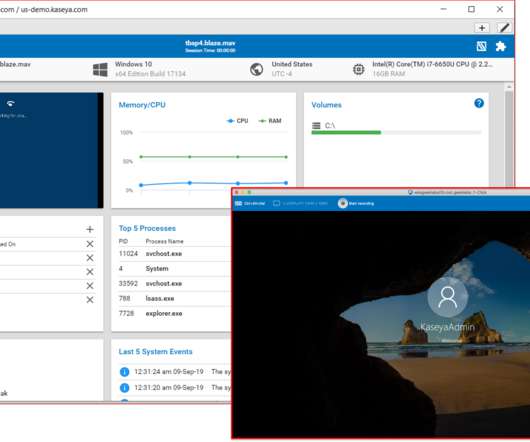
Kaseya
JANUARY 23, 2020
Kaseya Unified Backup (KUB) enables IT technicians to manage endpoints, monitor network devices, and perform backup and recovery tasks, all from a single pane of glass i.e. from Kaseya VSA, the endpoint and network management solution. . With the rise in ransomware attacks, having a unified backup solution in place is a must have.

Kaseya
FEBRUARY 14, 2023
In 2022, 71% of companies worldwide were affected by ransomware , with 62.9% of ransomware victims paying the ransom. Network analysis and reporting: This task involves measuring data transmission efficiency using latency, jitter, packet loss and throughput metrics. Threats are not only increasing in number but also complexity.
O'Reilly Media - Ideas
APRIL 5, 2022
Developers claim that Polycoder is better than Copilot for many tasks, including programming in C. BazarBackdoor [sic] is now believed to be under development by the Conti ransomware group. The attackers attacked: A security researcher has acquired and leaked chat server logs from the Conti ransomware group.

The Parallax
JUNE 26, 2018
TEL AVIV—If you listen to doctors who faced the WannaCry ransomware attack on the front lines of emergency rooms across England last year, it’s a minor miracle that the inadequate care it caused didn’t result in any patient deaths. Such a policy would mimic “the way that other companies secure a network from the Internet.”.
O'Reilly Media - Ideas
SEPTEMBER 1, 2021
Elon Musk announces that Tesla will release a humanoid robo t next year; it will be capable of performing tasks like going to the store. Amazon, Google, Microsoft, and others join the US Joint Cyber Defense Collaborative to fight the spread of ransomware. Apple will be scanning iPhones for images of child abuse.
Expert insights. Personalized for you.
Are you sure you want to cancel your subscriptions?

Let's personalize your content