Security and Privacy of COVID-19 Contact-Tracing Apps
Symantec
MARCH 12, 2021
Symantec analyzed the top 25 COVID-19 national contact-tracing apps to see which follow security and privacy best practices.
This site uses cookies to improve your experience. By viewing our content, you are accepting the use of cookies. To help us insure we adhere to various privacy regulations, please select your country/region of residence. If you do not select a country we will assume you are from the United States. View our privacy policy and terms of use.

 secure-contact-tracing
secure-contact-tracing 
Symantec
MARCH 12, 2021
Symantec analyzed the top 25 COVID-19 national contact-tracing apps to see which follow security and privacy best practices.

CIO
FEBRUARY 1, 2024
In today’s rapidly evolving cybersecurity landscape, having a proficient security team in place is not enough. IR sniping follows three main guiding principles: Low card exchange: Every contact leaves a trace. Artificial Intelligence, Security Organizations must understand the nuances of modern risks.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.

CTOvision
AUGUST 13, 2020
Read Ayal Yogev explain how companies can maximize data security by making sensitive data secure by default on Help Net Security : Consider the case of contact tracing, which has […].

TechCrunch
DECEMBER 22, 2020
ReturnSafe , a symptom checking and contact tracing employee health management toolkit for businesses, has raised $3.25 million in financing from investors including Fifty Years and Active Capital. .
The Parallax
MAY 28, 2020
Plummeting employee morale , a myriad mix of employee devices accessing the organization’s servers from home networks (all with hard-to-know security statuses), and hard-to-monitor employee data security practices have put employers’ data at greater risk than ever before. How to make your Zoom meetings more secure.
The Parallax
MAY 14, 2020
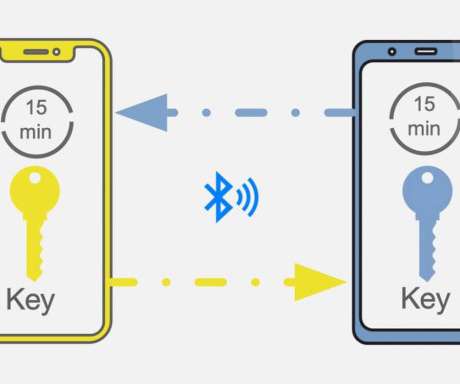
But manual contact tracing requires boots on the ground — people to track down patients, interview them about where they’ve been and with whom they’ve met, then find those people and let them know that they’ve been in contact with someone who has tested positive. How to make your Zoom meetings more secure.

Hacker Earth Developers Blog
SEPTEMBER 25, 2023
This article was written by Alwayne Powell, the Senior Digital Marketing Manager at 8×8 contact centre and communication platform. It aggregates complex telemetry data—metrics, logs, and traces—from disparate systems and applications in your business. You can find them on LinkedIn.
The Parallax
MAY 15, 2020
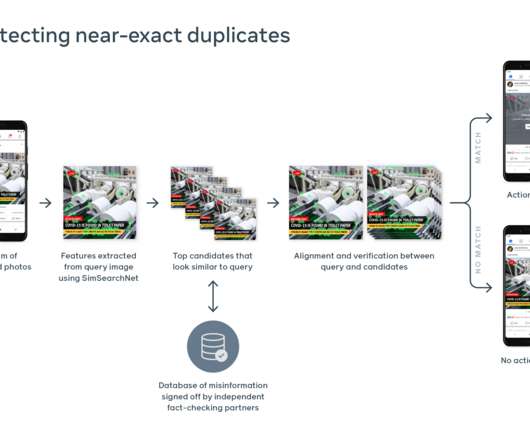
Secure contact tracing needs more transparent development. How to make your Zoom meetings more secure. READ MORE ON COVID-19 AND CYBERSECURITY. Phishers target oil and gas industry amid Covid-19 downturn. Hydroxychloroquine misinformation makes way for political disinformation.

The Parallax
MAY 29, 2020
Secure contact tracing needs more transparent development. How to make your Zoom meetings more secure. Remember Stasi spying to understand the GDPR. Facebook fails to curb coronavirus misinformation. Hydroxychloroquine misinformation makes way for political disinformation.

Capgemini
AUGUST 11, 2020
They require new sanitization routines, contact-less procedures, and to monitor temperature and other symptoms as well as monitor travel history or potential virus exposure for their crews. Additionally, operations managers need to conduct contact tracing if a crewmember falls sick. Taking the next step.

O'Reilly Media - Ideas
JUNE 23, 2020
Work From Home Cybersecurity Course — Secure your home Wi-Fi; Strong passwords; VPNs; Protecting confidential information; Personal devices; Phishing. On Contact Tracing and Hardware Tokens — Singapore recently gave a bunch of security people access to their TraceTogether token. who need this basic info.
Perficient
JANUARY 6, 2023
Service Cloud Voice Permissions and Security Explained. Essentially what this does for a business is two things: It streamlines the process of creating a fully integrated contact center software capable of saving your data and re-using it at a later time. Great, so now what? Well, the short answer is no!

Netlify
SEPTEMBER 7, 2021
Detecting anomalies in visitor activity including traffic from bots and bad actors to enable security and compliance engineers to proactively defend their sites. Please contact us through our forums , support channels , our Twitter account @Netlify , or fill out this short survey and share your thoughts with us today!

KitelyTech
FEBRUARY 26, 2021
The wearables can cross-check your location with everyone around you to trace potential individuals who might carry the virus. . The WHO has urged all health authorities to detect, test, trace and isolate any person with contracted coronavirus. Wearables have already made it to the healthcare facilities and college campuses.

Sunflower Lab
MARCH 25, 2024
Power BI, a powerful business intelligence tool by Microsoft, offers a vast number of security features and dashboards to ensure data protection, compliance, and risk mitigation. Power BI Security Dashboards provide organizations with the tools needed to monitor, manage, and enhance the security of their data assets.

Tenable
JUNE 23, 2022
This group has been examining vulnerabilities affecting OT security for a few years now and has produced notable findings including: NUCLEUS:13 , NAME:WRECK , NUMBER:JACK and AMNESIA:33. Phoenix Contact. Use secure methods for remote access when that access is necessary to operations. SYSMAC Cx series Nx series.

Palo Alto Networks
JANUARY 14, 2022
This allows you to genuinely improve the organization’s security posture and resilience. Harness a Threat-Intel Informed Approach to Continuously Evolve Your Security Strategy. You should be able to trace decisions made about your defensive priorities to credible intelligence of threat actors currently undertaking attacks.

The Crazy Programmer
JULY 3, 2022
When you study in the UK, you’ll have access to an extensive network of industry contacts. The university’s roots can be traced back as far as 1785. Every day, you’ll improve your written and spoken English skills as well as your ability to interact with others in a group setting. Work Experience.

CTOvision
APRIL 9, 2015
A look back at 2014 reveals any number of breaches that can be traced back to malicious or exploited insiders. Interestingly enough, Palo Alto Networks is working on ways to help its customers leverage the high fidelity data coming out of its Enterprise Security Platform. By Dan Cybulski.

Datavail
MAY 13, 2020
Deadlock Trace Flags. Deadlock trace flags, when enabled, ensure that the details of the deadlock are captured in the error log for later analysis. Trace flags 1204 and 1222 capture the deadlock node and query details. If you’re looking for SQL Server support for your organization, contact us to learn more. RECONFIGURE.

Openxcell
JUNE 1, 2023
Hackers can easily trace private keys on these hot wallets since they are online, 24*7. The use of cold storage wallets ensures the security of cryptocurrency holdings and is referred to as cold storage in the crypto world. Security The highest level of security for crypto assets is offered by cold wallets.

Tenable
SEPTEMBER 30, 2021
Thanks to Satnam Narang from the Security Response Team for his contributions to this blog post. Power Apps portals, as Microsoft describes them , allows both internal and external individuals to securely access Microsoft Dataverse data using portals. IBM X-Force Cloud Security Threat Landscape Report for Q2 2020 through Q2 2021.

Mobilunity
JULY 16, 2021
DevOps professionals can also be busy with one of the following roles: Evangelist/consultant; Release manager; Automation expert; Software developer; QA and XA expert; Security DevOps. It is crucial to implement the most advanced security measures in the CI/CD pipeline. Contact Our Team! CI CD DevOps Resume Sample.

Existek
JUNE 20, 2023
It handles user management, authentication flows, and secure access to Firebase resources. It provides a simple API for uploading and downloading files, and the files are automatically stored in a secure and scalable manner. Cloud Firestore is another NoSQL document database offered by Firebase.

Honeycomb
OCTOBER 21, 2021
Prior to joining Honeycomb, Andy was the Field CTO of application security observability provider TrueFort, Inc. Contact: Andy Hawkins. +44 Andy has proven success in leading high-growth teams and will lead Honeycomb’s expansion in the region to grow and scale local support for European customers. 44 7795464517.
TechCrunch
JULY 14, 2021
” The idea for the platform came after Orlic and his co-founders realized they could trace key career decisions to a handful of short conversations — brief moments of advice that ended up profoundly influencing the trajectory of their working lives, to the point where they were still looking back on them years later. ”).

CIO
JUNE 7, 2023
A tremendous number of enterprises and service providers view Cisco as the nexus of their network, security, and cloud operations. Cisco Secure Access. Generative AI to empower security and productivity. The Cisco Security Cloud leverages a generative AI assistant that addresses two use cases.

Openxcell
AUGUST 7, 2023
The initial roots of AI were traced back to the mid-’90s, with the pioneering work of Alan Turning, who embarked on experimenting and discovering the potential of machines to emulate human intelligence. Heightened security AI is vigilant to monitor large data applications, promptly detecting fraud and highlighting malicious activities.

Tenable
JULY 20, 2022
Nonetheless, many security analysts, researchers and reporters have examined the information available and developed insights into the group’s characteristics and tactics. Circumventing MFA through spamming prompts or contacting help desk. Bolster cloud security posture: improve risk detections, strengthen access configurations.
Altexsoft
JULY 14, 2021
How to secure PHI to stay HIPAA-compliant. Some of the identifiers include: names, locations, age, dates, contacts, and IDs. An appointment note to see a doctor usually contains the patient’s name and contact information. How to secure PHI to stay HIPAA-compliant. Introduce security systems and activity logs.

Cloudera
FEBRUARY 17, 2021
By making it part of CDP, not only do you just get the simplicity of 1 SKU to purchase but you also get the benefits of CDP and its unified security and governance layer – Cloudera SDX. The best part is that we bundled all this into the CDP Streaming Edition, which also includes Apache Flink.

Altexsoft
APRIL 13, 2023
Supply chain visibility is basically the detailed knowledge of every operational activity as it entails the ability to track and trace all the goods (inventory, parts, raw materials, etc.) Supply chain traceability is about tracing the complete lifecycle of goods. Data security. Let’s clear them up to get a better picture.

Altexsoft
OCTOBER 27, 2022
For an exact quote, you have to contact the provider directly. For exact rate estimation, contact the provider directly. The two top-tier plans give access to additional tools like Track&Trace which allows you to monitor the shipment status or the cross-docking feature for advanced warehousing and yard management operations.

Cloudera
SEPTEMBER 9, 2020
If you do not have a CDP AWS account, please contact your favorite Cloudera representative, or sign up for a CDP trial here. Since securing the cluster may utilize CM Auto TLS, Knox, Kerberos, and Ranger, ‘Spark submit’ may be dependent on aspects not covered in this post. You have environments and identities mapped and configured.
Mobilunity
APRIL 19, 2021
Contact Mobilunity and you’ll get professional help! Contact us. This question evaluates the candidate’s experience and the ability to trace back why a project succeeded or failed. Hire a UX/UI consultant to create an easy-to-use, good-looking website — contact Mobilunity to get a professional review of your project!

Cloudera
SEPTEMBER 18, 2020
Supply chain visibility – COVID may accelerate deployment of IoT devices, data, and analytics to improve real-time visibility across the entire supply chain from a ‘track and trace’ perspective. A greater emphasis on real-time visibility will drive greater planning precision. . Michael Ger: . The importance of real-time data.

TechCrunch
SEPTEMBER 20, 2022
But Atlas sank without a trace , while founder (and Napster co-founder) Jordan Ritter dropped off my radar after it until a couple weeks ago, when Augment reached out to talk about what amounts to the next generation of the idea, with a decidedly more modern approach. . “Hold on,” I hear you typing.

Modus Create
JULY 28, 2021
Example: Let us use the relative locators and find some of the elements on the Contact page of the Modus Create website. You can use the development properties such as Fetch, Network, Profiler, Performance, Application cache, Resource timings, Security, Target CDP domains, and debug the problems. Relative Locators Methods.
Xicom
OCTOBER 15, 2021
In a nutshell, pay securely and safely with GoPay. Allow users to register by updating their credentials like age, profile picture, payment method chosen and contact information. These days, real-time tracking features allow users to trace the location of the service providers easily. User Perspective. Registration.

CableLabs
AUGUST 20, 2019
Schurz Communications can trace its roots to 1872, when Alfred B. Through Otava, Schurz provides world-class cloud, colocation, data protection, disaster recovery, security and other professional services solutions to thousands of customers around the world. Schurz Communications: A Family Business That Values Meaningful Connections
Altexsoft
MARCH 16, 2021
People travelling around the country contact others and transmit infection. These included: Smart contact tracing with the help of GPS data, street cameras, credit card transactions, etc.; Data security and compliance concerns. A bright example is South Korea. Big Data in research.

Xicom
SEPTEMBER 25, 2019
Percent feeling secure to walk at night makes it the safest city in the world. Many security initiatives and projects helped to achieve this”. According to Dubai police officer, depending upon the severity of the chances of the case are there you won’t be contacted by the police unless it is a big case, no will disrupt you.

OverOps
JUNE 21, 2018
Application logs, security logs, BI logs, Lincoln logs (Ok, maybe not)… Setting aside security, BI and childhood fun for a moment, even looking specifically at uses for application logs alone, there are countless uses. Cloud: Contact for pricing info. Good for security, BI and infrastructure monitoring.

Altexsoft
SEPTEMBER 27, 2022
Contact information among all parties – contact details of all the parties involved. Airline-specific AWBs include the air cargo carrier’s details, i.e., name, logo, as well as head office address and contact details. track-trace or Ship24 ) to receive your shipment status details. Tracking cargo with Air India.
Expert insights. Personalized for you.
Are you sure you want to cancel your subscriptions?

Let's personalize your content