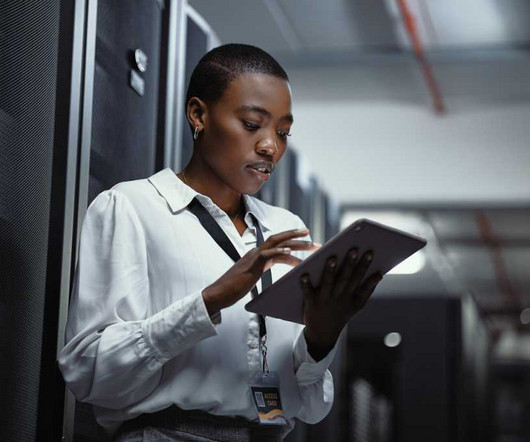
PCI compliance: Is your qualified security assessor up to the task?
CIO
OCTOBER 16, 2023
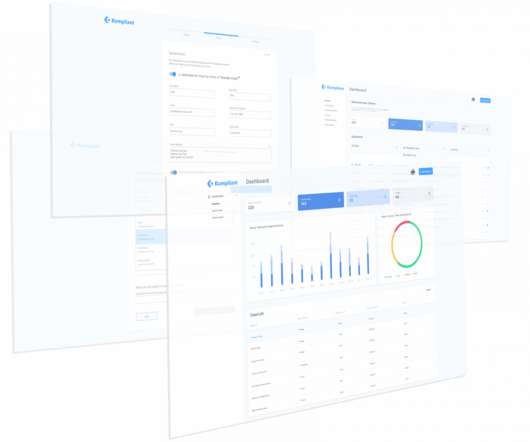
In a volatile payments landscape, enterprises are preparing for the Payment Card Industry Data Security Standard (PCI DSS) version 3.2.1 Understanding the changes in the Standard is paramount for Qualified Security Assessors (QSAs) to do a comprehensive and effective assessment,” adds Stachowicz. to expire on March 31, 2024.
















































Let's personalize your content