What Can We Do Differently About App Security?
TechBeacon
JUNE 15, 2023
Policymakers imposing TikTok bans have something to teach us about app security. But there are also more tools for app sec than the ban hammer.
This site uses cookies to improve your experience. By viewing our content, you are accepting the use of cookies. To help us insure we adhere to various privacy regulations, please select your country/region of residence. If you do not select a country we will assume you are from the United States. View our privacy policy and terms of use.

 what-can-we-do-differently-about-app-security
what-can-we-do-differently-about-app-security  Security Related Topics
Security Related Topics 
TechBeacon
JUNE 15, 2023
Policymakers imposing TikTok bans have something to teach us about app security. But there are also more tools for app sec than the ban hammer.

The Crazy Programmer
JULY 18, 2021
Cybersecurity is more critical than ever in today’s modern world, especially with news of ransomware attacks and other forms of malware on the rise. To keep your systems secure and your files out of the hands of cybercriminals takes an increasingly comprehensive knowledge of cybersecurity technology. Zero Trust.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.

CIO
SEPTEMBER 29, 2022
With the global pandemic upending the traditional way we work, employees across every market sector in New Zealand are now spending their workdays alternating between offices, their homes and other locations. The sheer number of smart devices in our lives means we are more vulnerable than we think.

CIO
FEBRUARY 14, 2024
Fundamentals like security, cost control, identity management, container sprawl, data management, and hardware refreshes remain key strategic areas for CIOs to deal with. When you think about all the blocking and tackling a CIO needs to do for regular applications, that especially applies to AI.”

TechEmpower CTO
JULY 24, 2023
At TechEmpower, we frequently talk to startup founders, CEOs, product leaders, and other innovators about their next big tech initiative. It’s part of our job to ask questions about their plans, challenge their assumptions, and suggest paths to success. After all, that’s what tech innovation is all about.
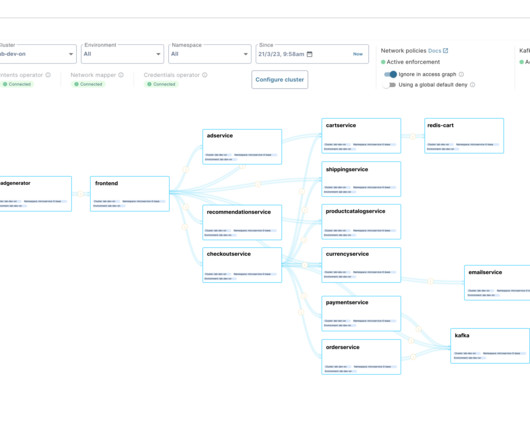
TechCrunch
APRIL 13, 2023
Tomer Greenwald, Uri Sarid and Ori Shoshan, software developers by trade, found themselves building and configuring software authentication and authorization mechanisms repeatedly — each time with a different tech stack. Otterize today raised $11.5

CIO
APRIL 18, 2024
Before I get to why, what even is a “cloud native platform”? A platform not only runs that software, but it manages the services your apps need. Typically, the platform also specifies how your apps are packaged, configured, and deployed to your platform. The platform usually has opinions about your app’s architecture.

CIO
NOVEMBER 14, 2023
There are so many people who bought into cloud without thinking through the real reasons why they were doing this and what they wanted to accomplish,” says David Mitchell Smith, distinguished vice president and analyst at Gartner focused on cloud computing and digital foundations. Why are we really going to cloud?

CIO
FEBRUARY 22, 2023
But while the cloud provides more flexible and scalable IT services, it’s also introducing new and vexing challenges around cyber security. The recent attacks on NFPs would seem to highlight many of the security risks being posed by the migration to the cloud.

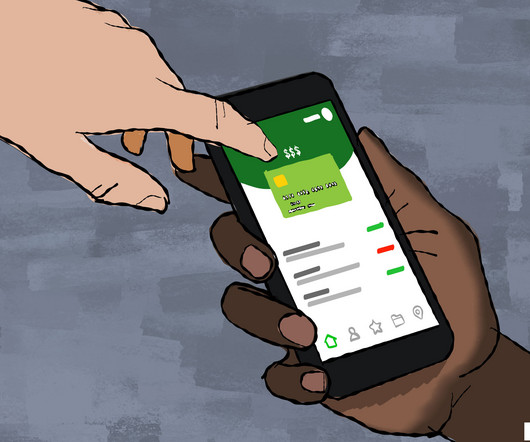
The Crazy Programmer
JANUARY 17, 2024
The scenario changed during the lockdown period when people had nothing much to do than focus on different types of apps. Now, business owners, whether small or big, want to release mobile apps to establish their digital footprints. What Is Mobile App Security? Read on to know more. Have a look: 1.

Xebia
NOVEMBER 14, 2023
Security should be considered from the initial stages of designing a product rather than as an afterthought. Security requirements may vary depending on the use case; for instance, a banking solution would have different security needs compared to a solution for a local bakery. Initially, it was TLS 1.0,

CIO
NOVEMBER 16, 2023
Generative AI is transforming the world, changing the way we create images and videos, audio, text, and code. A large language model (LLM) is a type of gen AI that focuses on text and code instead of images or audio, although some have begun to integrate different modalities. Dig Security addresses this possibility in two ways.

CIO
APRIL 17, 2024
Suddenly, you can create engaging customer-facing videos at the click of a button,” says Oliver Banks, retail consultant and author of Driving Retail Transformation: How to navigate disruption and change. But what we’re learning from public announcements like these might just scratch the surface of gen AI use cases for the enterprise.
TechCrunch
NOVEMBER 17, 2021
The cloud may be the direction that much of enterprise IT is moving today, but it still remains a major source of security issues, with some 98% of all enterprises in a recent survey reporting that they have contended with a cloud-related security breach in the last 18 months. Shaked worked for some time at Magic Leap.

CIO
FEBRUARY 13, 2023
This includes spending on strengthening cybersecurity (35%), improving customer service (32%) and improving data analytics for real-time business intelligence and customer insight (30%). CIOs anticipate an increased focus on cybersecurity (70%), data analysis (55%), data privacy (55%), AI/machine learning (55%), and customer experience (53%).

CIO
APRIL 12, 2024
Shoppers can find overalls, live chickens, gun safes, ice fishing augers, ferret food, throw blankets, a farmhouse-shaped egg holder , and welding machines as they walk the aisles of most Tractor Supply stores. Customers may have questions about plants to grow in a certain climate zone, for example.

CIO
JANUARY 5, 2023
However, low code/no code is not a silver bullet for all application types and can require costly rewriting if a customer underestimates the degree to which applications must scale or be customized once they reach production. So there’s a lot in the plus column, but there are reasons to be cautious, too.
TechCrunch
MARCH 29, 2023
Thousands of founders have applied to land capital through a common app, Natasha M reports. The app is then blasted to 16 investors. Autio, a location-based audio entertainment app co-founded by actor Kevin Costner and formerly known as HearHere, has raised $5.9 Ask Sophie: What to do if selected/not selected in H-1B lottery?

Ivanti
FEBRUARY 13, 2024
The connection to DEX may not have entirely been clear, until I explained that his ability to easily do his work remotely using online tools exemplifies what good DEX is all about in the era of Everywhere Work. In our own research , we found that 31% of IT professionals were still using spreadsheets to track IT assets.

TechCrunch
MARCH 30, 2023
Given the damage bots can do — for example, stealing content and inventory, degrading website and app performance, taking over accounts and committing payment fraud — it’s not exactly surprising that vendors selling bot-fighting tech are attracting big investments. So what makes DataDome different?

Tenable
DECEMBER 1, 2023
Plus, a new survey shows generative AI adoption is booming, but security and privacy concerns remain. In addition, CISA is warning municipal water plants about an active threat involving Unitronics PLCs. cybersecurity agencies to publish this week a joint document titled “ Guidelines for Secure AI System Development.” “We
Xebia
JANUARY 30, 2023
During this blog series we are going to look at different types of Application Security Testing (AST), Software Composition Analysis (SCA) and secret scanning. They are used to identify security vulnerabilities in applications. After the explanation we will get our hands dirty and try out some tools manually.

CIO
AUGUST 24, 2023
It can also expose companies to future legislation. These complaints, filed by a variety of different copyright holders, allege the companies of training their AIs on copyrighted data—images, code, and text. In July, for example, New York City started enforcing new rules about the use of AI in hiring decisions.
Xebia
FEBRUARY 17, 2023
Introduction Welcome to part two of the Application Security Testing series. Like I mentioned in the previous blog, during this blog series we are going to look at the different types of Application Security Testing and Software Composition Analysis. This time we will focus on Dynamic Application Security Testing (DAST).
Xebia
JUNE 19, 2023
Introduction Welcome to part three of the blog series about Application Security Testing. In part one of this series, we looked at Static Application Security Testing (SAST) and in part two at Dynamic Application Security Testing (DAST). First a brief explanation is given about IAST.

TechCrunch
JUNE 1, 2021
The cybersecurity industry has no shortage of technology to fight against network intruders, app corrupters, email hackers and other cyber criminals. Ten Eleven is a VC specializing in cybersecurity that has backed a number of other startups.) His co-founder, John Hering, was the founder and CEO of cybersecurity firm Lookout.

CIO
AUGUST 25, 2022
Having many hundreds of interconnected devices in what we now call edge environments is nothing new. What’s different now is that the concept of what will comprise a network node is changing rapidly, along with the number of interconnected devices. Secure code for the edge.

CIO
AUGUST 24, 2023
Think about what the world will look like in five, 10, or even 15 years. Let’s dive into what that looks like and how you can get started now. But today, every customer and prospect I speak with is thinking about how generative AI (GenAI) can benefit their business. The bottom line?

Tenable
AUGUST 19, 2020
Independent business risk study shows cybersecurity is seldom fully integrated into business strategy – and it needs to be. The first question she asks you is: “How secure are we?” . If you’ve spent more than a minute in cybersecurity, you know why answering this question is far more challenging than it might seem. .

Palo Alto Networks
OCTOBER 12, 2020
For many, this means fall festivities and pumpkin spice, but in the cybersecurity industry we look forward to a month of driving cybersecurity awareness. While using new technologies and apps and navigating school in a virtual environment can seem overwhelming, cybersecurity doesn’t have to be.

CIO
AUGUST 29, 2022
Board directors like Jean Holley can be a CIO’s best friend or worst nightmare. On three different boards, directors have asked Holley if the company chose the right CIO, and three times her answer was no. The CEO and board may steer the ship, but they’re relying on the CIO’s radar to see what’s coming. Don’t be that CIO.

CIO
JANUARY 24, 2023
Furthermore, the firm had predicted that the number of hybrid workers would continue to increase, hitting 55% as we enter 2023. He advises CIOs to partner with their counterparts in HR to identify the worker archetypes that exist in their organizations to understand how they work and what they need to succeed.

TechCrunch
APRIL 1, 2021
Every tech vendor has to pass security muster with customers, typically a tedious activity involving answering long questionnaires. After company co-founder and CEO Sravish Sridhar sold his previous startup Kinvey , which provided backend as a service to mobile app developers, he took a couple of years off while he decided what to do next.

Palo Alto Networks
OCTOBER 31, 2023
Extending Code to Cloud™ Platform with Innovative Data Security for the Generative AI Era The digital landscape is undergoing a profound shift. As many large enterprises rely on hybrid cloud and multicloud environments, it is becoming increasingly challenging to know with confidence whether or not your data is secured.

CIO
NOVEMBER 28, 2022
The survey explores changes from the collective experience of the last two years that business decision-makers should pay attention to as we are introduced to ‘Free Dimensional’ work, and what was a temporary fix during the pandemic. We all have a unique hybrid work/life balance that works for each of us.
TechCrunch
MARCH 8, 2023
Much of the focus today is on TikTok, the viral video-sharing app owned by Chinese firm ByteDance, which faces bans over fears that the data it collects will end up in the hands of the Chinese government. It’s not an unreasonable fear, especially with over a billion users worldwide using the app.
TechCrunch
AUGUST 12, 2022
More funding for European end-to-end encrypted messaging app, Wire : The enterprise-focused messaging platform told TechCrunch it closed a €24 million Series C round of funding led by growth equity firm Cipio Partners and Iconical, the investment vehicle of Skype co-founder Janus Friis.

CIO
OCTOBER 31, 2022
During these visits, I’ve also answered their questions and shared our vision of what a combined Broadcom and VMware will look like following the close of the transaction. Ultimately, what I’ve stressed to them has been straightforward: our customers are and will remain the most important part of our business. I’ll share an example.

CIO
JULY 6, 2023
The hybrid IT architecture is here to stay, according to F5’s 2023 State of Application Strategy Report , and that has profound implications for how enterprises should be thinking about modernizing, deploying, and securing applications. By 2020, that number had dropped to about one-fourth of respondents.
TechCrunch
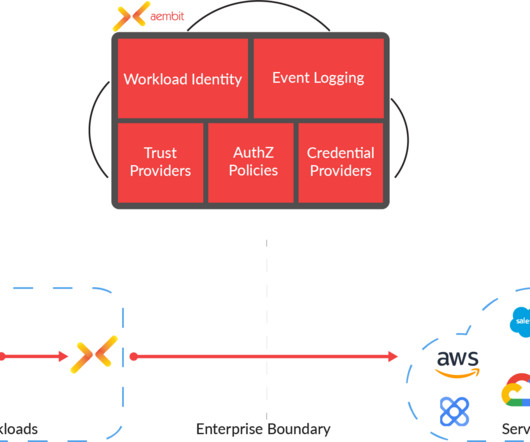
MARCH 20, 2023
Aembit , a Maryland-based security startup that focuses on helping DevOps and security teams manage how federated workloads talk to each other, is officially launching its service today and announcing a $16.6 “Along the way, people would always ask us: what about workload-to-workload application-level access?

CIO
DECEMBER 21, 2023
The diversification of payment methods and gradual increase in the volume of online transactions have cast a spotlight on the need for payment security compliance within the airline industry. With the new, recently onboarded Payment Card Industry Data Security Standard (PCI DSS) v4.0, Well not exactly. The PCI DSS v4.0, The PCI DSS v4.0,

CIO
JUNE 5, 2023
Tapping an app on a mobile device at home relies on many connections. Count them: the home Wi-Fi, the ISP, the Internet, a Domain Name System (DNS) provider, a content delivery network (CDN), applications distributed among multiple providers in multiple clouds, credit authentication companies, a private customer information database.

Openxcell
NOVEMBER 28, 2023
Enterprise application security is one of the most important aspects of protecting organizations from external attacks. Over the years, cybersecurity vulnerability reports have recorded an increase in the number of security holes in enterprise applications. What is Enterprise Application Security?

CIO
JANUARY 5, 2024
Having led Radisson Hotel Group’s IT on a global scale for more than three years, what milestones have you achieved? Also during the pandemic, we completely restructured and created every IT element the company needed: new ERP, purchasing systems, hotel management systems, and HR systems, for example.
Expert insights. Personalized for you.
Are you sure you want to cancel your subscriptions?

Let's personalize your content