
The U.S., China and Avoiding World War III
SUBSCRIBER+ EXCLUSIVE INTERVIEW — A new leader takes power in Taiwan, Taiwan and China hold competing military drills, the rhetoric from both sides grows increasingly […] More

As part of a week-long series focused on Mapping China’s Ambitions, The Cipher Brief is partnering with Harvard Research Fellow and former British diplomat Jamie Burnham to explore China’s threat vectors, how it is organizing to win, what a government ecosystem looks like and the impact that international collaboration will have in the future.
Yesterday in The Cipher Brief, Jamie explored China’s broad ambitions and threat vectors, today, he focuses on how Beijing is organizing against those ambitions and threat vectors.
Jamie Burnham, Research Fellow, Harvard Kennedy School’s Belfer Center for Science and International Affairs

Jamie Burnham is a research fellow at the Harvard Kennedy School’s Belfer Center for Science and International Affairs where he is exploring how digital technologies are changing political intelligence and policy-making. As a British diplomat, he served across Africa and the Middle East, with specific interests in weapons technology proliferation and the resilience of fragile states.
The government’s information architecture will have to be re-configured to meet the challenge posed by the Chinese state. Some of the policy responses are already maturing, most notably in the strengthening of the law governing commercial transactions in high priority technology sectors. The UK’s national security and investment bill introduces a hybrid system of mandatory and voluntary notifications on the grounds of national security. A more muscular application of existing tools such as export control orders is apparent. The Times newspaper reported that more than ‘200 UK citizens at more than a dozen universities’ were to receive export control enforcement notices. However, policy tools are ineffectual – and potentially damaging – if they are not supported by intelligence. Government requires timely insight in order to be less reactive, deliver earlier and less costly interventions, and exploit the global diplomatic and intelligence network to protect UK interests overseas. The modern data environment gives advantage to those who learn how to break down compartmentalized activity and share knowledge.
IDENTIFYING INTENT
The PRC’s intent in technology acquisition is well signalled. It is both strategic and pragmatic and rooted in historical behaviours. There is a long-term visible ‘desire to meet, by whatever means are necessary, the strategic goals of the time – whatever they may be – while at the same time building a system that can eventually self-perpetuate and be self-sufficient.’ Doctrine papers demand a whole of society approach to achieving a common aim. ‘Made in China 2025’, for example, seeks to upgrade Chinese industry so that it can occupy the highest parts of global supply chains and identifies ten priority sectors, including new advanced information technology; automated machine tools and robotics; aerospace and aeronautical equipment; maritime equipment and high technology shipping; modern rail transport equipment; new energy vehicles and equipment; power equipment; agricultural equipment; new materials and bio-pharma and advanced medical products.
While the broad outlines are clear, it requires more specialist skills and capabilities to identify the technology gaps that the PRC is targeting. Approaches might include:
IDENTIFYING CAPABILITY
Technology acquisition networks are complex and diffuse. Relationships are often informal or opaque. It requires investigative techniques, combined with advanced analytical tooling, to identify the systems which pose risk. Established analytical approaches include:
AN EXAMPLE OF DATA MODELING
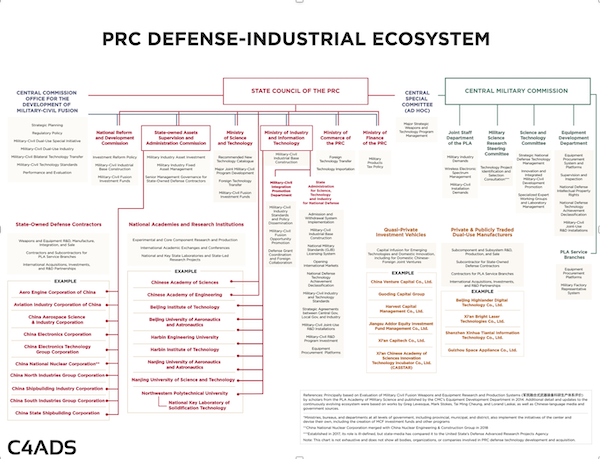
The Washington DC-based think-tank C4ADS has modelled PRC acquisition networks in the defence sector. This may provide a useful model for other technology areas. The doctrine of Military-Civil Fusion (MCF) under Xi Jinping has evolved long-standing concepts of military and civilian collaborative activity into a sophisticated eco-system. Commercial technologies are leveraged to develop military capability. The civilian industrial base participates in defence technology supply chains. Dedicated funds allocate capital for defence innovation. Conferences and trade fairs bring together defence contractors and dual use manufacturers. Industrial zones incubate new technologies.
C4ADS used data on PRC commercial and state organisations to identify four broad types of actor involved in overseas defence technology acquisition. A network diagram is at Figure 1. Using advanced data modelling techniques, they were able to identify:
Having developed a model of defence acquisition networks, C4ADS were able to further illuminate their role in importing materials and technologies into the PRC. C4ADS was able to identify 65,272 incidents of imports to the PRC between 2014 and 2019. 61% of these imports were for potentially dual use goods, with the US, Japan, Germany and South Korea emerging as the top suppliers. Had it been possible to identify the materials as being associated with the defence sector, export control licences might have been applied.
The Cipher Brief hosts private briefings with the world’s most experienced national and global security experts. Become a member today.
ORGANISING TO WIN
To assume that ‘big data’ and AI will somehow easily meet your purpose, is to fail. The technology is not the challenge: organisational culture, fixed mental models and institutional boundaries are. Intelligence officers – whose lives are spent cloistered behind secretive walls – often struggle to comprehend that there might be information of value or interest in the real world. Shaped by the bitter truths of the Cold War, they have learned that knowledge hidden, is more advantageous than knowledge shared. In the world of hybrid competition, however, data is leaking across the matrix of globalised infrastructure. To ignore it, is to be blind. To isolate from networks that receive and share it, is to be deaf and dumb. Intelligence agencies may evolve into ‘knowledge platforms’ which collect information of value rather than sensitivity, and deploy skills in exploitation, analysis and delivery of impact.
SPONSORSHIP
Change within any organisation requires sponsorship. This is not simply a question of governance or budgeting. Developing an analytics eco-system, like other elements of government digital transformation, requires operating across institutional boundaries, building new operational models and challenging fixed assumptions. The urgency of crises and the need to deliver a succession of quick tactical fixes can preclude longer-term change within departments, allowing strategic debt to accumulate. The success of the UK’s Government Digital Service rested not just on the outstanding leadership of its founders, but the active support of Francis Maude, the Cabinet Office Minister. They recognised the need for a sponsor who understood the high costs of leaving the status quo alone. ‘Delivering change in the face of inertia takes a lot of time and energy as well as political capital.’ Any new capability must have the support of a senior leader who is personally committed to its success.
PEOPLE
People remain the most valuable ingredient. The skillsets required for data analysis are demanding. The UK government is blessed by analytical talent. Digital analysis, however, requires an evolution of the skillset. At the heart of analysis will remain the classic approaches demanded in making sense of complexity. David Omand terms these as the SEES: Situational awareness, Explanation of events and motivations, Estimates and forecasts, and Strategic notice of long-term strategic issues. Being able to frame the right question will always be hard – and the question will almost certainly have to be refined as the problem becomes better understood.
Digital analysis, however, poses additional challenges. Conventionally, analysts may determine patterns from established data sets, such as intelligence reports, media reporting or academic journals. However, the digital analyst faces the daunting task of searching for data in the infinite vastness of the internet, unclear about what to select or what patterns to look for. Each data set is likely to be of significant scale, have gaps and be structured uniquely. Above all, much of it is in a foreign language. There are plenty of pitfalls. Answers may look credible but in fact be wrong, perhaps because the wrong data was selected, or the cultural or linguistic context has been misunderstood, or the question was insufficiently defined.
Unpicking these challenges requires multi-disciplinary teams. A requirements specialist must engage with the broader government community to understand the policy or operational drivers and help frame the questions. Data scientists must develop statistical models and adapt analytical systems. Analysts must understand the context in which information sits and be able to interrogate it to find answers.
Organisational culture is fundamental to success. Assumptions must be challenged, and creativity and ingenuity applauded, if new pathways are to be discovered. Hierarchies must therefore be flat. A diversity of lived experience must be encouraged. No individual will arrive fully formed. People must be trained and mentored in order to flourish. Teams must be small in order to foster mutual trust and self-organize to find solutions. Individuals must develop broader social networks to leverage intellectual capital and fresh ideas.
TOOLS
The scale of data available and the challenge in making sense of it requires highly advanced analytical tools. The problems of large-scale data handling are not unique to government and the commercial sector is developing significant capabilities. Operating on the ‘low-side’ has costs associated with the procurement of new capabilities and infrastructure, but these are marginal compared to the challenges of in-house capability development necessary within in the intelligence community. The information architecture, and audit and security standards, may accord with commercial best practice. Indeed, one advantage of operating outside classified ‘high side’ systems is to trial new techniques and technologies, without risking compromise of secrets.
The systems should have the following characteristics:
DATA
Traditional intelligence models place heavy focus on sensitive collection techniques, which are necessary but also slow and expensive. As information increases in availability and costs reduce, insight that was once the preserve of the state becomes readily available. The commercial world may watch North Korea’s nuclear programme from space or track mobile telephony. At the same time, maintaining secrecy becomes more demanding and more expensive. Data permits tracking of CIA spy aircraft in Iraq or Russian assassins in Salisbury. As publically available data becomes a tool of national security, it will itself evolve. Intelligence agencies, for example, will seek to conceal their activities by altering databases or by providing false information. Therefore the validation of data becomes a critical task.
In a ‘low-side’ domain, analysts may practise ‘data foraging’ by looking to the internet or commercial suppliers for valuable information. This provides the unique quality of speed. Commercial, academic and international partnerships may provide further data, analysis and techniques. An analytics capability should work to commercial norms and not seek data which is proprietary. Such data requires specific regulatory oversight and limits the dissemination (and therefore the impact) of information. Examples of the sorts of data that can be exploited include:
Read part three of The Cipher Brief Special Series on China with Harvard Fellow Jamie Burnham in tomorrow’s Cipher Brief. You can catch Part One: Ambitions and Threat Vectors here.
Read more expert-driven national security insights, analysis and perspective in The Cipher Brief
Related Articles

SUBSCRIBER+ EXCLUSIVE INTERVIEW — A new leader takes power in Taiwan, Taiwan and China hold competing military drills, the rhetoric from both sides grows increasingly […] More

SUBSCRIBER+ EXCLUSIVE REPORTING — The U.S. and its allies in the “Five Eyes” intelligence-sharing community – Britain, Australia, Canada and New Zealand – warned Wednesday […] More

SUBSCRIBER+ INTERVIEWS — As the North Atlantic Treaty Organization (NATO) marks its 75th anniversary, it is also marking what is arguably the most important moment […] More

SUBSCRIBER+EXCLUSIVE INTERVIEW — In all of U.S. military history, few events have depended more on secrecy and subterfuge than Operation Overlord, which was launched on […] More

SUBSCRIBER+EXCLUSIVE INTERVIEW — The International Atomic Energy Agency (IAEA) is holding its Board of Governors meeting this week, just days after the agency reported that […] More

SUBSCRIBER+ EXCLUSIVE – It may be President Biden’s most consequential decision about the Ukraine war since Russia’s February 2022 invasion: allowing Ukraine to strike Russian […] More
Search