Why nontechnical organizations need due diligence
Synopsys
JULY 14, 2023
Software impacts tech and nontech businesses alike, which is why a strategic acquirer or PE firm always needs due diligence.
This site uses cookies to improve your experience. By viewing our content, you are accepting the use of cookies. To help us insure we adhere to various privacy regulations, please select your country/region of residence. If you do not select a country we will assume you are from the United States. View our privacy policy and terms of use.
Synopsys
JULY 14, 2023
Software impacts tech and nontech businesses alike, which is why a strategic acquirer or PE firm always needs due diligence.

Synopsys
MAY 26, 2023
Organizations should emphasize processes that connect the dots between software development practices, business risk and due diligence activities.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.

CIO
DECEMBER 28, 2023
The need to manage risk, adhere to regulations, and establish processes to govern those tasks has been part of running an organization as long as there have been businesses to run. This level of complexity requires a robust GRC framework to assist an organization with avoiding reputational damage and legal penalties.” What is GRC?

OTS Solutions
JUNE 21, 2023
However, as more organizations rely on these applications, the need for enterprise application security and compliance measures is becoming increasingly important. Breaches in security or compliance can result in legal liabilities, reputation damage, and financial losses.

TechCrunch
NOVEMBER 8, 2022
Compliance with privacy and security frameworks like SOC 2, HIPAA and GDPR has become a central component not just of how organizations build trust with their users, but of how organizations work together these days: fail to meet the requirements of these frameworks, and you might lose your business relationship.

CIO
JANUARY 4, 2024
However, managing PCI security compliance across various lines of business within these institutions can be a complex and resource-intensive task. The CCA allows overarching enterprise functions and IT shared services to be assessed separately from the business unit’s products/applications that require PCI security compliance.

Xebia
NOVEMBER 1, 2023
InnerSource can be defined as the application of open-source software development principles within an organization’s internal software development processes. It draws on the valuable lessons learned from open-source projects and adapts them to the context of how companies create software internally. What is InnerSource?

Synopsys
JANUARY 3, 2022
Similar to a home inspection, M&A software due diligence helps organizations assess the risk of an investment. The post Manage risks with software due diligence and open source audits appeared first on Software Integrity Blog.

CIO
NOVEMBER 17, 2022
By Milan Shetti, CEO Rocket Software In today’s fast-paced digital business world, organizations have become highly adaptive and agile to keep up with the ever-evolving demands of consumers and the market. Let’s take a closer look at the essential features cloud-first businesses should look for in a content management software.

Cherry Work
MAY 2, 2024
A few procedures in the world of business operations may not make news, but their influence on the success of organizations is clear. Businesses may face difficulties due to inefficient invoice management, which can result in payments being delayed, disputes with suppliers and penalties. One such example is invoice management.

OTS Solutions
JUNE 21, 2023
However, as more organizations rely on these applications, the need for enterprise application security and compliance measures is becoming increasingly important. Breaches in security or compliance can result in legal liabilities, reputation damage, and financial losses.
Erik Bernhardsson
DECEMBER 12, 2023
Some of the advice is timeless, for instance the section about “General interference with Organizations and Production”: Insist on doing everything through “channels” Never permit short-cuts to be taken in order to expedite decisions. It laid out various ways for infiltrators to ruin productivity of a company.

CIO
DECEMBER 8, 2023
They don’t present big problems if you’re noodling around with gen AI prompts at home, but in enterprise organizations that are deploying new chatbots to huge numbers of customers and employees, just one AI fabrication can land companies in court. In IT organizations, gen AI glitches wreak havoc in other ways. Deploy content filters.

OverOps
JUNE 4, 2019
The following is a guest post from Herb Krasner, an Advisory Board Member for the Consortium for IT Software Quality (CISQ) and industry consultant for 5 decades. In a previous post , we looked at the magnitude and impact of the soaring cost of poor software quality in the US and where those hidden costs are typically found.

CIO
MARCH 18, 2024
Compliance with DORA will require full adherence to five critical areas of focus outlined in the regulation: ICT risk management : This guidance establishes a standard framework for what organizations should do in response to an ICT security incident. Is your IT security infrastructure ready for future regulations?

Hacker Earth Developers Blog
MARCH 19, 2024
Assessment software has come a long way from its humble beginnings. Key Features of Assessment Software: Accuracy : Precision is non-negotiable. The best software allows for tailored assessments, aligning with specific objectives and criteria. Customization : Flexibility is key.

Hacker Earth Developers Blog
MARCH 19, 2024
Assessment software has come a long way from its humble beginnings. Key Features of Assessment Software: Accuracy : Precision is non-negotiable. The best software allows for tailored assessments, aligning with specific objectives and criteria. Customization : Flexibility is key.

CEO Tech Tips
JULY 25, 2021
M&A mergers and acquisitions typically involve a significant amount of due diligence including what obligations it is assuming, the nature and extent of the seller’s contingent liabilities, problematic contracts, litigation risks, intellectual property issues, and much more. What software is critical to the seller’s operations?

Modern CTO
DECEMBER 11, 2023
Today we’re talking to Matt van Itallie, Founder & CEO at Sema Software. We discuss the risks surrounding AI generated code, how to circumvent those risks with smarter software decisions, and we also get to catch up on life with Matt and Joel. To try Sema’s code monitor, click here. His motivation?

CIO
NOVEMBER 21, 2023
By no means a quick and easy transformation, it requires addressing two sides of the equation at once: the demand side in how IT manages technology requests and the supply side in how technology requirements are vetted and reviewed against appropriate solutions.

CircleCI
JULY 18, 2022
Software development teams face a large and growing number of obstacles: shifting design requirements, organizational blockers, tight deadlines, complicated tech stacks and software supply chains. Compliance requirements can add significant overhead to an organization. Examples of software compliance requirements.

CIO
MAY 4, 2023
Now let’s take a closer look at how data privacy and sovereignty regulations are driving security, privacy, and compliance. Multi-national companies frequently rely on in-country compliance experts to help ensure they’re following the latest rules correctly and to avoid significant fines and legal action.

Dzone - DevOps
NOVEMBER 21, 2023
A DevOps service company can play a crucial role in assisting organizations with meeting ISO 27001 and GDPR compliance requirements by integrating security and compliance into their DevOps workflows. This guarantees quick responses to potential threats or breaches, which is vital for GDPR compliance.

CIO
FEBRUARY 7, 2024
Most companies have transitioned to become more software-centric, and with this transformation, application programming interfaces (APIs) have proliferated. API-first strategies on the rise APIs are ubiquitous within modern software architectures, working behind the scenes to facilitate myriad connected capabilities. “As

Abhishek Tiwari
JULY 22, 2023
In the fast-paced world of software development, the ability to deploy applications quickly and efficiently is crucial for organizations. However, amidst the drive for speed, ensuring policy compliance is often overlooked, leading to potential security vulnerabilities and compliance risks.

CIO
MARCH 15, 2023
Restructuring can create uncertainty and stress in an organization, and it shouldn’t be used lightly or regularly, Sinclair explains. He notes that IT organizations can usually work through almost any problem as long as the parties grow together. Change requires something that is stable and durable.”

Perficient
MARCH 26, 2024
Accessibility compliance is crucial to providing equal access to all users, including those with disabilities. Importance of Accessibility Compliance Accessibility compliance ensures that websites are usable by individuals with disabilities, such as vision impairments, mobility issues, or cognitive challenges.

TechCrunch
OCTOBER 21, 2020
While certifications for security management practices like SOC 2 and ISO 27001 have been around for a while, the number of companies that now request that their software vendors go through (and pass) the audits to be in compliance with these continues to increase. But it’s just what our customers needed.

CIO
SEPTEMBER 11, 2023
Scaled Agile Framework (SAFe) explained The Scaled Agile Framework encompasses a set of principles, processes, and best practices that helps larger organizations adopt agile methodologies , such as Lean, Kanban, and Scrum , to deliver high-quality products and services faster. Decentralize decision-making to become more agile and effective.

Apiumhub
JANUARY 18, 2024
Software deployment best practices are crucial for ensuring the smooth and reliable release of software. This frequency is a pivotal value stream metric and a fundamental benchmark within the core DORA metrics, providing insights into your software delivery efficiency. Git) for both code and configuration files.

Datavail
FEBRUARY 28, 2024
Given that Oracle is one of the world’s leading providers of database technology, many mid-market and enterprise organizations rely on its solutions for managing and processing crucial data. There are many ways in which you can unwittingly fall into non-compliance or waste resources.

CIO
FEBRUARY 14, 2024
Generative AI continues to dominate IT projects for many organizations, with two thirds of business leaders telling a Harris Poll they’ve already deployed generative AI tools internally, and IDC predicting spend on gen AI will more than double in 2024. But the usual laundry list of priorities for IT hasn’t gone away.

CIO
MAY 2, 2024
As a result, Siemens Mobility learned that UiPath could help it automate processes involving different software applications, with a focus on SAP integration. “We Our main aim is to enable, motivate, and engage our colleagues within the organization to apply RPA themselves,” he says. “We
CIO
NOVEMBER 13, 2023
By cross-training operations and engineering, development teams can move faster through better collaboration, making continuous integration and continuous delivery (CI/CD) a reality for organizations. With Rocket® DevOps , organizations can perform multiple tests seamlessly and speed up time-to-market for high-quality releases.

Xebia
SEPTEMBER 14, 2021
Using common software, functionalities can be purchased and integrated with the click of a button and the availability of a credit card. Value-stream teams have been given more autonomy and possibilities to select, purchase and integrate hardware and software. Organizing architecture guided by two perspectives.

CIO
SEPTEMBER 12, 2023
Generative AI has taken the world seemingly by storm, impacting everything from software development, to marketing, to conversations with my kids at the dinner table. Copyright Issues: Enterprise employees use Generative AI to create content such as source code, images, and documents.

Kaseya
MAY 19, 2022
IT compliance refers to a set of statutory rules and regulations that businesses must follow to minimize the threat of a cyberattack and keep their systems and processes secure. Every organization must adhere to industry standards and regulations relevant to their business. What is IT compliance? What is a compliance standard?

Newgen Software
OCTOBER 28, 2023
Cut to present, this is exactly what your organization also needs. A robust Business Process Management (BPM) software that automates your end-to-end processes of day-to-day operation. What is Business Process Management Software (BPM)? Furthermore, it helps gain real-time insights and minimize errors.

Perficient
MARCH 13, 2023
However, its preconfigured security can be insufficient in regulating or monitoring confidential information due to the flexibility it offers. Policy-as-code is a way to automate data security and privacy controls, allowing organizations to apply centralized policies to data science and analytics projects.
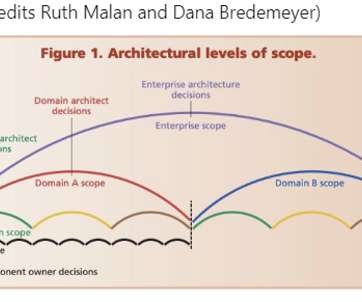
Xebia
AUGUST 3, 2021
Using common software, functionalities can be purchased and integrated with the click of a button and the availability of a credit card. Value-stream teams have been given more autonomy and possibilities to select, purchase and integrate hardware and software. Organizing architecture guided by two perspectives.

CIO
DECEMBER 11, 2023
AI has whet the appetites of organizations across nearly every sector. Organizations must also consider what values guide them, and what obligations they have in terms of retraining, upskilling, and job protection. Here is a look at how CIOs are addressing ethical AI in their organizations.
TechCrunch
MAY 13, 2021
SpecTrust aims to “fix the economics of fighting fraud” with a no-code platform that it says cuts 90% of a business’ risk infrastructure spend that responds to threats in “minutes instead of months.” . “In Don’t hate on low-code and no-code.

Tenable
APRIL 16, 2024
As has become crystal clear in recent years thanks to events like Log4j’s Log4Shell vulnerability and the SolarWinds breach, software supply chain security is critical. At Tenable, protecting our software supply chain is a top priority. Ensuring the integrity of software artifacts across your entire software supply chain.

CIO
MARCH 7, 2023
Kellen, CIO at the University of California San Diego (UCSD), says employees are already using ChatGPT to write code as well as job descriptions. The models respond to written requests to generate a variety of responses ranging from text documents and images to programming code. That’s incredibly powerful.”
Expert insights. Personalized for you.
Are you sure you want to cancel your subscriptions?


Let's personalize your content