What you need to know about Okta’s security breach
CIO
OCTOBER 25, 2023
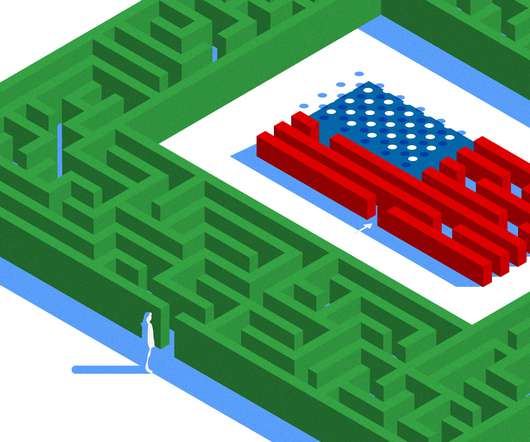
Traditional security controls are bypassed in such attacks as bad actors assume a user’s identity and their malicious activity is indistinguishable from routine behavior. In this recent OKTA breach, no reports suggest major incidents so far. HAR files often contain sensitive data that malicious actors can use to imitate valid users.











































Let's personalize your content