How to Choose an OT Cybersecurity Solution Vendor
Tenable
NOVEMBER 4, 2021
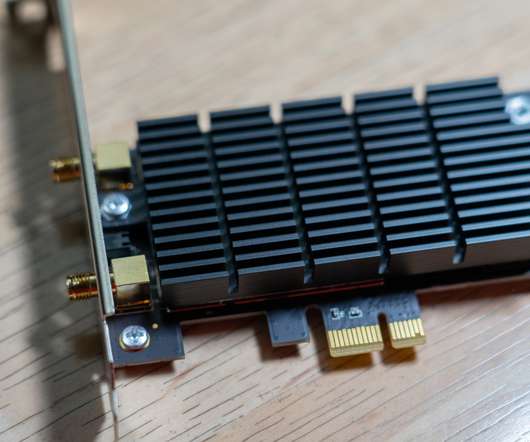
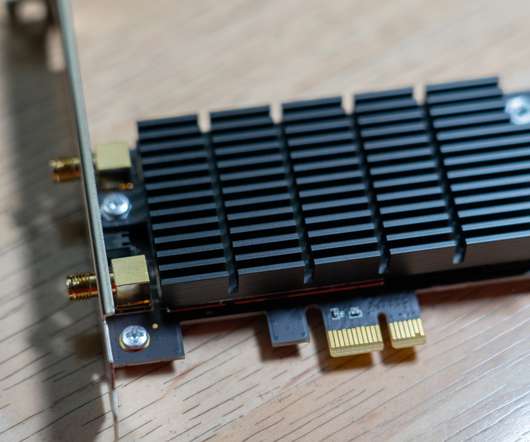
As cyberattacks in critical infrastructure, such as those on the Colonial Pipeline, make headlines, cybersecurity experts must address the risk that this esoteric environment poses to their company. includes Nessus to allow deep inspection of the security posture of these devices and common operating systems when it is safe to do so.





















Let's personalize your content