Elusive Chinese Cyberspy Group Hijacks Software Updates to Deliver Malware
Ooda Loop
JANUARY 29, 2024
The Chinese cyberespionage group, Blackwood, has been caught delivering malware to entities in China and Japan.
This site uses cookies to improve your experience. By viewing our content, you are accepting the use of cookies. To help us insure we adhere to various privacy regulations, please select your country/region of residence. If you do not select a country we will assume you are from the United States. View our privacy policy and terms of use.

Ooda Loop
JANUARY 29, 2024
The Chinese cyberespionage group, Blackwood, has been caught delivering malware to entities in China and Japan.

Ooda Loop
APRIL 9, 2024
The threat group behind a complex JavaScript remote access Trojan (RAT) known as JSOutProx has released a new version of the malware to target organizations in the Middle East. Resecurity, a cybersecurity services firm, is analyzing technical details of multiple instances of the malware targeting financial customers.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.

CIO
AUGUST 24, 2022
The “sting” of a ransomware or malware attack is removed quickly, efficiently, and comprehensively. Who would have thought that the latest answer to cyberattacks was actually found in guaranteed cyber recovery on primary storage?

SecureWorks
DECEMBER 9, 2022
Type: Blogs Drokbk Malware Uses GitHub as Dead Drop Resolver A subgroup of the Iranian COBALT MIRAGE threat group leverages Drokbk for persistence. A subgroup of the Iranian COBALT MIRAGE threat group leverages Drokbk for persistence.

CTOvision
NOVEMBER 23, 2020
A new variant of a skimmer has revealed the increasingly muddy waters associated with tracking groups involved in Magecart-style attacks. On Wednesday, researchers from RiskIQ described how a new Grelos […].

Lacework
JULY 15, 2022
This ancient technique has found its place in the world of malware, namely hiding malicious code within other files including image formatted files ( T1027.003 ). This blog takes a look at the latter technique in recent cryptojacking activity from a group known as WatchDog. Steg malware is uncommon relative to other malware.

SecureWorks
MARCH 8, 2022
Type: Blogs Excel Add-ins Deliver JSSLoader Malware The GOLD NIAGARA threat group has expanded its tactics for delivering the JSSLoader RAT, spoofing legitimate Microsoft Excel add-ins to infect systems. Learn how CTU researchers observed multiple malicious Microsoft Excel add-ins delivering JSSLoader malware.

Tenable
MARCH 3, 2023
FBI and CISA Release Cybersecurity Advisory on Royal Ransomware Group The FBI and CISA have released a joint Cybersecurity Advisory discussing the Royal ransomware group. The advisory details the tactics, techniques and procedures associated with the group and indicators of compromise associated with infection.

Ooda Loop
MAY 24, 2024
The hacking group has remained under the radar since 2018 using new and improved tools, tactics, and techniques (TTPs). A Chinese threat actor, Unfading Sea Haze, has been targeting military and government entities in South China Sea countries for at least six years, Bitdefender reports. The threat actor has been […]

Symantec
APRIL 20, 2022
Russia-linked group is continually refining its malware and often deploying multiple payloads to maximize chances of maintaining a persistent presence on targeted networks.

Ooda Loop
DECEMBER 12, 2023
Cisco researchers recently observed the North Korea-linked Lazarus hacking group deploy three Dlang malware families against various targets in the manufacturing, agriculture, and physical security sectors.

Tenable
MAY 18, 2023
and Australian Agencies Publish Joint Cybersecurity Advisory on BianLian Ransomware Group The FBI, ACSC and CISA have released a joint cybersecurity advisory discussing the BianLian ransomware group. The group claims to have stolen ~4,200 student records containing phone numbers, email addresses, and social security numbers.

Ooda Loop
FEBRUARY 15, 2024
Microsoft’s threat intelligence team recently partnered with OpenAI to produce a report on threat actors using LLMs to streamline vulnerability research, targeting, and malware development.

Tenable
AUGUST 4, 2022
Analyzing the Vulnerabilities Associated with the Top Malware Strains of 2021. International cybersecurity agencies issue a joint alert outlining the top malware strains of 2021. While malware is used for a variety of purposes, the government agencies point out that ransomware is a primary use case. Background. Description.

Ooda Loop
APRIL 23, 2024
According to a Microsoft report, Russian-linked cybercrime group APT28 has been exploiting Windows Print Spooler vulnerabilities to deploy an exploitation tool against organizations across Western Europe, in Ukraine, and in the US.
Tenable
JANUARY 27, 2023
Sandworm APT Deploys New SwiftSlicer Wiper Using Active Directory Group Policy Sandworm, the Russian-backed APT responsible for NotPetya in 2017, has recently attacked an Ukrainian organization using a new wiper, SwiftSlicer. Attackers deployed a new wiper we named #SwiftSlicer using Active Directory Group Policy.

Ooda Loop
FEBRUARY 15, 2024
Group-IB, a cybersecurity company based in Singapore, recently attributed the development of sophisticated banking trojans to Chinese-speaking cyber crime group GoldFactory. The threat group has previously […] The threat group has previously […]

TechCrunch
JULY 20, 2022
Meanwhile, Carly writes that Google Drive is in the spotlight after it was found that Russian hackers are using the software to hide malware. One story touches on the company’s not-so-good news about losing subscribers , and the other two stories provide an update on its ad-supported tier and an acquisition of Animal Logic.

Symantec
FEBRUARY 22, 2023
No custom malware deployed in attack campaign that appears to rely exclusively on open-source tools.

Symantec
OCTOBER 10, 2018
A new attack group is targeting government, military, and defense sectors in what appears to be a classic espionage campaign.

Tenable
JULY 20, 2022
Having gained the industry’s attention in the first months of 2022, the LAPSUS$ extortion group has largely gone quiet. What can we learn from this extortion group’s story and tactics? In early 2022, the LAPSUS$ group broke onto the scene with flashy and disruptive attacks. Who is the LAPSUS$ group?

Symantec
FEBRUARY 8, 2023
Russia-linked Nodaria group has deployed a new threat designed to steal a wide range of information from infected computers.

Tenable
APRIL 25, 2024
Who is the group behind ArcaneDoor? The group has been labeled UAT4356 by Cisco and STORM-1849 by Microsoft. Cisco attributes this activity with “high confidence” to a state-sponsored actor, though it is unconfirmed which state the group is associated with. Is any malware associated with ArcaneDoor?

CTOvision
DECEMBER 12, 2018
A cyber espionage group is deploying a new type of trojan malware against telecommunications, information technology, and government organisations.

Ooda Loop
APRIL 18, 2024
Mandiant published a new report summarizing the latest activities of Russia’s Sandworm group, also known as APT44. Sandworm is one of the most notorious Russian threat actor groups, conducting espionage, disruption, and disinformation campaigns. Recently, […]
Darktrace
NOVEMBER 18, 2020
As the US Treasury announces new sanctions on the Russian institute believed to be behind the TRITON malware, this blog takes a look at the significance of this attack, and extrapolates what’s around the corner for OT cyber-attacks.

CIO
MARCH 13, 2023
By Ram Velaga, Senior Vice President and General Manager, Core Switching Group This article is a continuation of Broadcom’s blog series: 2023 Tech Trends That Transform IT. It’s also been flagged as a risk: cybersecurity companies have identified bad actors using ChatGPT to create malware. But how good can it be?

Ooda Loop
APRIL 11, 2024
‘EXotic Visit’, an Android malware campaign has been targeting users located in South Asia from the Google Play Store. No known threat actor group is linked to the campaign. The cybersecurity firm Slovak has been tracking the campaign since November 2021 using the moniker Virtual Invaders. EXotic Visit is also […]

Tenable
APRIL 12, 2024
1 - CISA to federal agencies: Act now to mitigate threat from Midnight Blizzard’s Microsoft email hack Midnight Blizzard, a nation-state hacking group affiliated with the Russian government, stole email messages exchanged between several unnamed U.S. military have had access to Malware Next-Generation Analysis since November.

Ooda Loop
MARCH 22, 2024
Security researchers at Mandiant have raised concerns after discovering that Russia’s APT29 hacking group, linked to the country’s foreign intelligence service (SVR), has begun targeting political parties in Germany. The attack involves multi-stage malware, including phishing […]

CIO
MAY 15, 2024
A model trained on, say, an archive of flat earth conspiracy theories will be bad at answering science questions, or a model fine-tuned by North Korean hackers might be bad at correctly identifying malware. They’re also full of inaccurate and biased information, malware, and other materials that can degrade the quality of output.

Tenable
MARCH 1, 2024
Plus, the latest guidance on cyberattack groups APT29 and ALPHV Blackcat. And the most prevalent malware in Q4. government is alerting healthcare companies in particular about the threat from the ALPHV Blackcat ransomware-as-a-service (RaaS) group, which this week claimed responsibility for an attack against Change Healthcare.

SecureWorks
SEPTEMBER 8, 2022
Type: Blogs BRONZE PRESIDENT Targets Government Officials The likely Chinese government-sponsored threat group uses decoy documents and PlugX malware to compromise targets. The likely Chinese government-sponsored threat group uses decoy documents and PlugX malware to compromise targets.

Tenable
AUGUST 25, 2023
That’s according to the study “The State of Cybersecurity Today” from Information Services Group (ISG), for which 204 executives from the world’s 2,000 largest companies were polled. Among respondents, 24% were C-level executives, such as CISOs and CIOs. on average in 2023 compared with 2022. “We

Symantec
SEPTEMBER 9, 2021
Group has heavy focus on telecoms sector. Recent campaigns involved exploits against Exchange and MySQL servers.

The Parallax
FEBRUARY 18, 2020
SAN FRANCISCO—The greatest trick stalkerware, one of the most dangerous forms of malware , ever played was convincing the world that it didn’t exist. Until recently, cybersecurity experts could overlook stalkerware because of the personal nature of how it spreads, its muddled legal status—and how it is detected.

AlienVault
DECEMBER 17, 2018
In part 1 of this blog series, we analyzed malware behaviour, and, in part 2 , we learned how to detect persistence tricks used in malware attacks. We can add a group condition with an OR operator inside to match the case. Still, there are more types of events that we can observe with Osquery when malicious activity happens.

Palo Alto Networks
DECEMBER 29, 2022
23, a new variant of wiper malware, named HermeticWiper, was discovered in Ukraine. Russia’s Gamaredon aka Primitive Bear APT Group Actively Targeting Ukraine. The Gamaredon group (aka Trident Ursa, Primitive Bear) is one of the most active, advanced and persistent threats (APT) targeting Ukraine. Top Malware.

Darktrace
NOVEMBER 17, 2020
As the US Treasury announces new sanctions on the Russian institute believed to be behind the TRITON malware, this blog takes a look at the significance of this attack, and extrapolates what’s around the corner for OT cyber-attacks.

Lacework
JUNE 7, 2022
As of this writing we have observed active exploitation by known Cloud threat malware families such as Kinsing, “Hezb”, and the Dark.IoT botnet. One interesting development was the use of a new malware host – 195.2.79.26 Several malware components were observed, the first of which was an XMRig miner installed as “Hezb”.

The Parallax
JANUARY 22, 2018
Its success was predicated not on “zero-day” vulnerabilities or new forms of malicious software, but rather on older, known malware delivered via an all-too-familiar method: phishing. The malware included hacked versions of end-to-end encrypted communication apps Signal and WhatsApp.

CIO
SEPTEMBER 29, 2022
As a result, the potential for malware to become resident on home computers is increasing.”. We regularly educate our employees about the potential of malware through scam emails, often alerting staff to current market scams as well as regular phishing exercises. In addition, most home computers are used by various family members.

Tenable
FEBRUARY 9, 2024
On February 7, researchers at Fortinet published a blog post highlighting the exploitation of CVE-2022-42475 and CVE-2023-27997 by Chinese threat groups including Volt Typhoon , APT15 (also known as Ke3chang) and APT31 (also known as ZIRCONIUM) as well as UNC757 ( also known as Fox Kitten), which has a “suspected nexus to the Iranian government.”
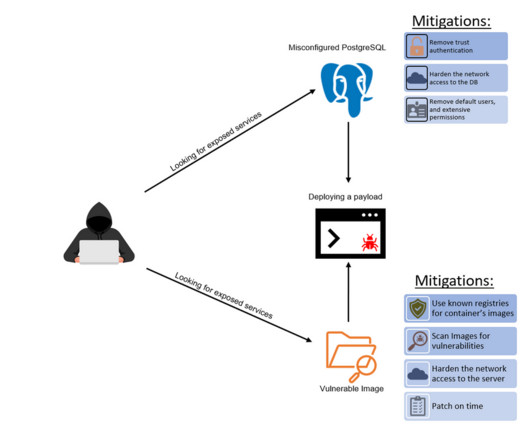
Lacework
FEBRUARY 7, 2024
Once the scanning process uncovers possible targets, the next phase is exploitation, where the threat actors deploy various forms of malware. Malware (e.g., In another, Obsidian discovered that the 0mega ransomware group carried out data extortion by gaining access to the admin account of a victim’s SharePoint account.
Expert insights. Personalized for you.
Are you sure you want to cancel your subscriptions?


Let's personalize your content