Why you must extend Zero Trust to public cloud workloads
CIO
NOVEMBER 8, 2023
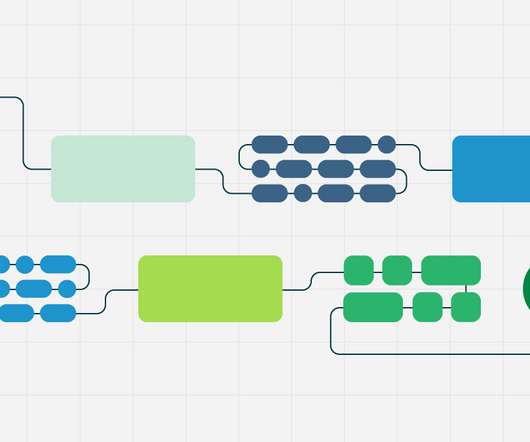
A recent study shows that 98% of IT leaders 1 have adopted a public cloud infrastructure. However, it has also introduced new security challenges, specifically related to cloud infrastructure and connectivity between workloads as organizations have limited control over those connectivity and communications. 8 Complexity.




























Let's personalize your content