How to manage cloud exploitation at the edge
CIO
JULY 17, 2023
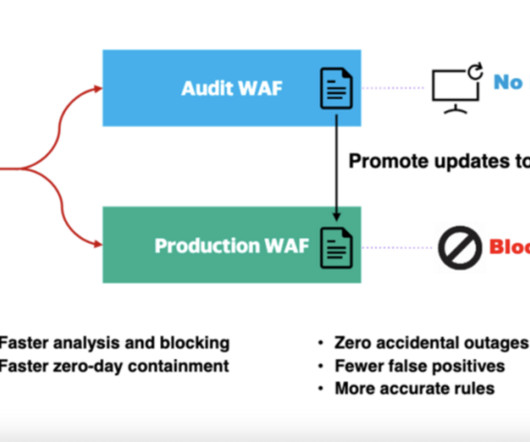
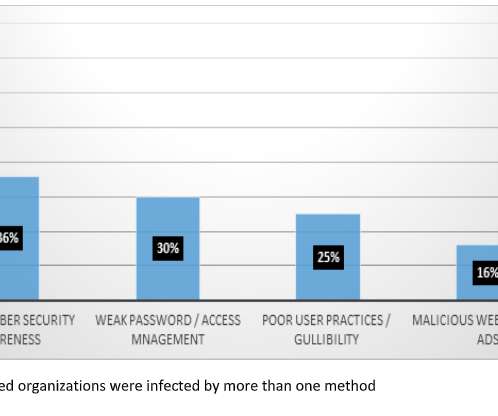
As with all technology introductions, it’s important to have clear security policies, tools, processes, and training. Malware Distribution: Cloud exploitation can involve hosting or distributing malware through cloud-based platforms or services. A powerful choice in the cyberthreat fight is a WAAP solution.















































Let's personalize your content