Microsoft’s May 2024 Patch Tuesday Addresses 59 CVEs (CVE-2024-30051, CVE-2024-30040)

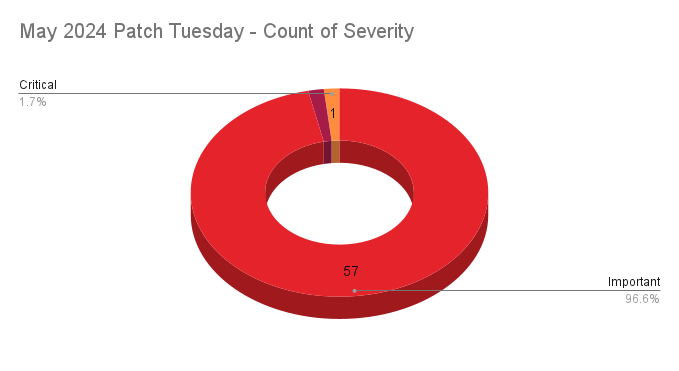
- 1Critical
- 57Important
- 1Moderate
- 0Low
Microsoft addresses 59 CVEs in its May 2024 Patch Tuesday release with one critical vulnerability and three zero-day vulnerabilities, two of which were exploited in the wild.
Microsoft patched 59 CVEs in its May 2024 Patch Tuesday release, with one rated critical, 57 rated as important and 1 rated as moderate. Two CVEs were excluded from our count (CVE-2024-32002, CVE-2024-32004) as they are GitHub assigned CVEs and not issued by Microsoft.
This month’s update includes patches for:
- .NET and Visual Studio
- Azure Migrate
- Microsoft Bing
- Microsoft Brokering File System
- Microsoft Dynamics 365 Customer Insights
- Microsoft Intune
- Microsoft Office Excel
- Microsoft Office SharePoint
- Microsoft WDAC OLE DB provider for SQL
- Microsoft Windows SCSI Class System File
- Microsoft Windows Search Component
- Power BI
- Windows Cloud Files Mini Filter Driver
- Windows CNG Key Isolation Service
- Windows Common Log File System Driver
- Windows Cryptographic Services
- Windows Deployment Services
- Windows DHCP Server
- Windows DWM Core Library
- Windows Hyper-V
- Windows Kernel
- Windows Mark of the Web (MOTW)
- Windows Mobile Broadband
- Windows MSHTML Platform
- Windows NTFS
- Windows Remote Access Connection Manager
- Windows Routing and Remote Access Service (RRAS)
- Windows Task Scheduler
- Windows Win32K - GRFX
- Windows Win32K - ICOMP
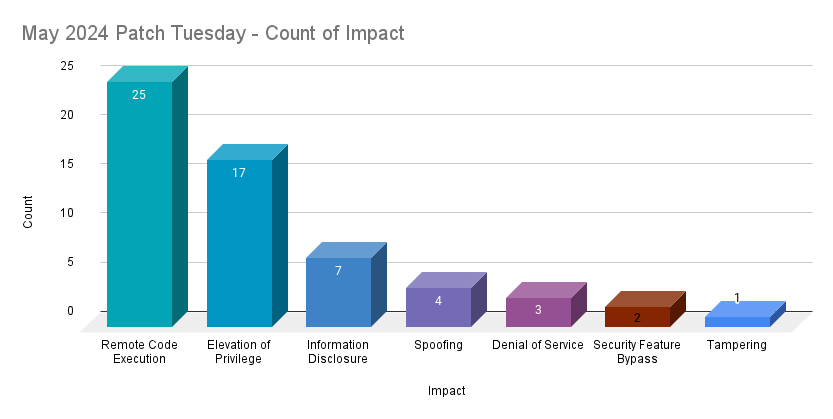
Remote code execution (RCE) vulnerabilities accounted for 42.4% of the vulnerabilities patched this month, followed by elevation of privilege (EoP) vulnerabilities at 28.8%.
CVE-2024-30051 | Windows DWM Core Library Elevation of Privilege Vulnerability
CVE-2024-30051 is an EoP vulnerability in the DWM Core Library in Microsoft Windows. It was assigned a CVSSv3 score of 7.8 and is rated as important. Microsoft noted that it was exploited in the wild as a zero-day and was publicly disclosed prior to a patch being available. A local attacker with a presence on a vulnerable system could exploit this vulnerability to gain SYSTEM privileges. Discovery of this flaw is credited to several researchers at Google Threat Analysis Group, Google Mandiant and Kaspersky. It is also credited to Quan Jin of DBAPPSecurity WeBin Lab, who disclosed CVE-2023-36033, another zero-day vulnerability in the DWM Core Library exploited in the wild that was patched in November 2023. Researchers at Kaspersky have linked this zero-day vulnerability to QakBot and other malware.
In addition to CVE-2024-30051, Microsoft patched two other EoP vulnerabilities in the DWM Core Library (CVE-2024-30032, CVE-2024-30035) and an information disclosure vulnerability (CVE-2024-30008). All three flaws were disclosed to Microsoft by Zhang WangJunJie and He YiSheng of the Hillstone Network Security Research Institute.
CVE-2024-30040 | Windows MSHTML Platform Security Feature Bypass Vulnerability
CVE-2024-30040 is a security feature bypass vulnerability in the MSHTML (Trident) engine in Microsoft Windows that was exploited in the wild as a zero-day. It was assigned a CVSSv3 score of 8.8 and is rated as important. An attacker could exploit this vulnerability by using social engineering tactics via email, social media or instant messaging to convince a target user to open a specially crafted document. Once exploited, an attacker could execute code on the target system. Discovery of this flaw is unattributed.
In 2023, there were eight vulnerabilities patched in MSHTML including three RCEs, four security feature bypass flaws and one EoP* (CVE-2024-32046) that was exploited as a zero-day:
| CVE | Description | Patched |
|---|---|---|
| CVE-2023-21805 | Windows MSHTML Platform Remote Code Execution Vulnerability | February 2023 |
| CVE-2023-29324 | Windows MSHTML Platform Security Feature Bypass Vulnerability | May 2023 |
| CVE-2023-35336 | Windows MSHTML Platform Security Feature Bypass Vulnerability | July 2023 |
| CVE-2023-35308 | Windows MSHTML Platform Security Feature Bypass Vulnerability | July 2023 |
| CVE-2023-32046* | Windows MSHTML Platform Elevation of Privilege Vulnerability | July 2023 |
| CVE-2023-36805 | Windows MSHTML Platform Security Feature Bypass Vulnerability | September 2023 |
| CVE-2023-36436 | Windows MSHTML Platform Remote Code Execution Vulnerability | October 2023 |
| CVE-2023-35628 | Windows MSHTML Platform Remote Code Execution Vulnerability | December 2023 |
CVE-2024-30046 | Visual Studio Denial of Service Vulnerability
CVE-2024-30046 is a denial of service (DoS) vulnerability affecting multiple versions of Microsoft Visual Studio 2022. It was assigned a CVSSv3 score of 5.9 and is rated important. It is listed as being publicly disclosed prior to a patch being made available. It is rated as “Exploitation Less Likely” according to Microsoft’s Exploitability Index and its Attack Complexity rating is listed as High. This is due to the fact that an attacker would need to “invest time in repeated exploitation attempts” through the sending of “constant or intermittent data” to a targeted system. DoS attacks often require a steady stream of requests in order to overwhelm a target system, so these ratings are expected.
CVE-2024-30044 | Microsoft SharePoint Server Remote Code Execution Vulnerability
CVE-2024-30044 is a RCE vulnerability in Microsoft SharePoint Server. It was assigned a CVSSv3 score of 8.8 and is rated critical. This vulnerability is rated as “Exploitation More Likely.” However, exploitation of this flaw requires an attacker authenticated to a vulnerable SharePoint Server with Site Owner permissions to perform two steps: 1.) the attacker must upload a specially crafted file to the vulnerable SharePoint Server and 2.) send specially crafted API requests to the SharePoint Server in order to “trigger deserialization of file’s parameters.” Successful exploitation would result in remote code execution “in the context of the SharePoint Server.”
Tenable Solutions
A list of all the plugins released for Tenable’s May 2024 Patch Tuesday update can be found here. As always, we recommend patching systems as soon as possible and regularly scanning your environment to identify those systems yet to be patched.
For more specific guidance on best practices for vulnerability assessments, please refer to our blog post on How to Perform Efficient Vulnerability Assessments with Tenable.
Get more information
- Microsoft's May 2024 Security Updates
- Tenable plugins for Microsoft May 2024 Patch Tuesday Security Updates
Join Tenable's Security Response Team on the Tenable Community.
Learn more about Tenable One, the Exposure Management Platform for the modern attack surface.
Related Articles
- Exposure Management
- Vulnerability Management
- Exposure Management
- Vulnerability Management





