Addressing the insecurity of verified identities
CIO
OCTOBER 20, 2023
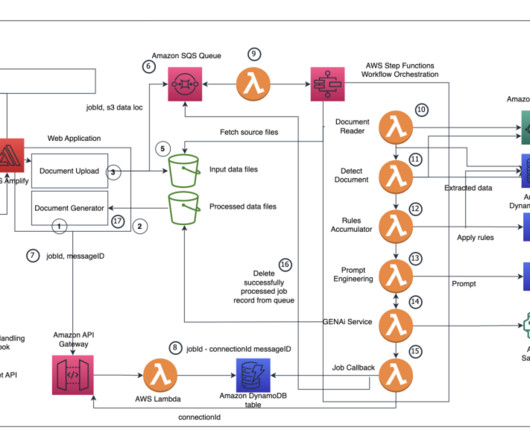
Intruders impersonate assets in Active Directory Suppose a malicious actor slips past your identity verification. Under some circumstances, attackers can use this technique to compromise the host Active Directory (AD) forest and then breach other connected forests.















































Let's personalize your content