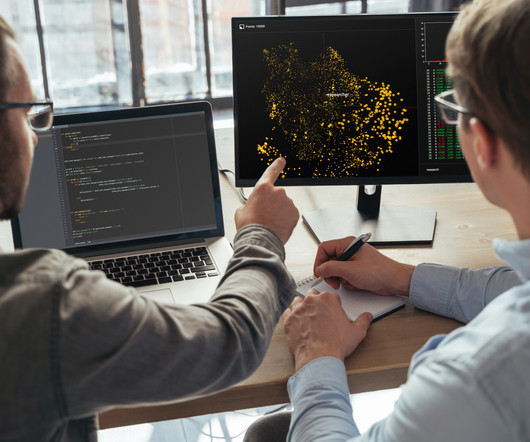
Connecting the dots of smart manufacturing and networking
CIO
JUNE 9, 2024
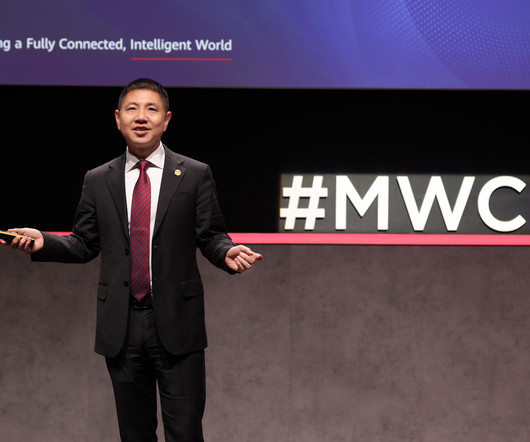
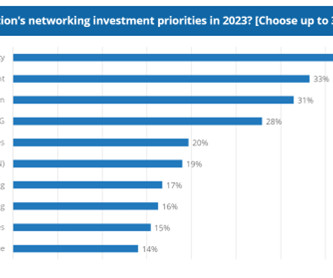
How an AI-driven network drives Industry 4.0 To find a place in this new technological frontier, proactive manufacturers must turn to AI-driven networks. According to Allied Telesis’ Senior Vice President Ozawa Tsuyoshi, network AI transcends simple definition as a mere algorithm. initiatives. and beyond Embracing Industry 4.0















































Let's personalize your content