How Watchdog smuggles malware into your network as uninteresting photos
Lacework
JULY 15, 2022
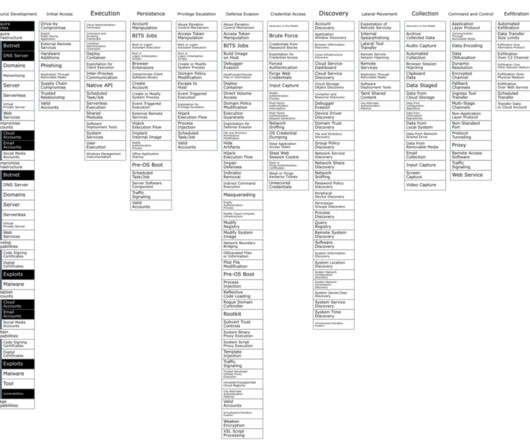
This ancient technique has found its place in the world of malware, namely hiding malicious code within other files including image formatted files ( T1027.003 ). The most widespread steg tactics are crude and involve using fake file extensions or file headers that are subsequently stripped by another component. Malware Details.












Let's personalize your content