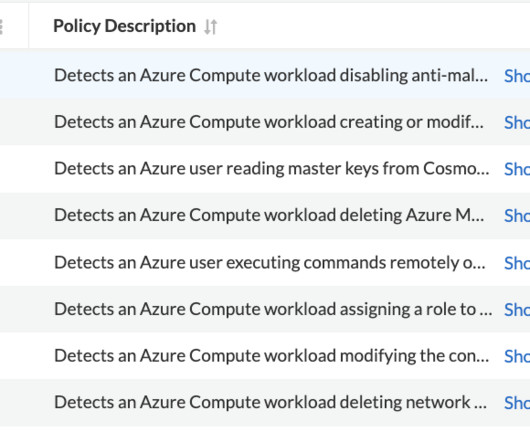
Azure-Specific Policies to Detect Suspicious Operations in the Cloud Environment
Prisma Clud
APRIL 20, 2023
Such operations allow bad actors to perform a range of attack techniques, such as lateral movement, credential access, and data exfiltration. The attacker could then use the permissions of the machine to modify the routing tables in the network and directly access a remote server to perform data exfiltration.














Let's personalize your content