Technical Review: A Deep Analysis of the Dirty Pipe Vulnerability
Aqua Security
DECEMBER 14, 2022
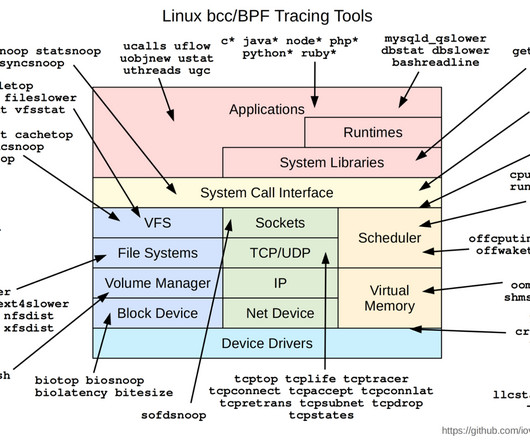
An application of this vulnerability would be to write on the host from an unprivileged container. In this blog we’ll show how Tracee, which is designed with a deep understanding of the Linux kernel, allows for runtime monitoring when this vulnerability would be exploited.














Let's personalize your content