How Cloud Security Influences IoT Security
Xebia
OCTOBER 27, 2022
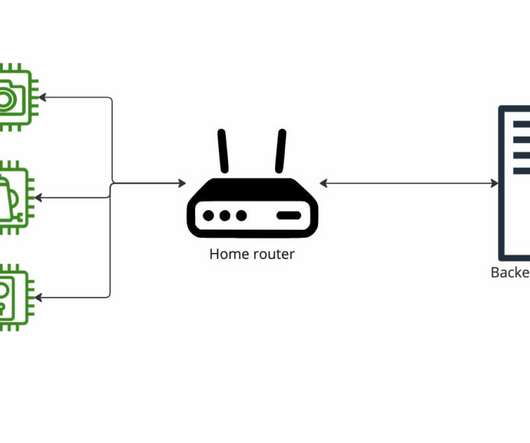
From a usability perspective this was incredible for developers and maintainers. Instead of compromising devices individually, they can compromise the central monitoring and management system to compromise all the managed devices through it. Is the system designed to identify malicious access and respond accordingly?


















Let's personalize your content