How Cloud Security Influences IoT Security
Xebia
OCTOBER 27, 2022
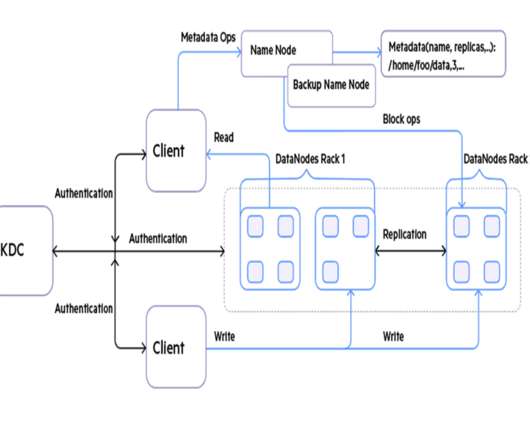
We conduct workshops regularly on this topic. How does authentication work? . . 509 certificate to authenticate while others have derived credentials based on unique device characteristics such as MAC addresses. Can a non-authenticated user access information on the service? Don’t know how to do that? Is it tested?

















Let's personalize your content