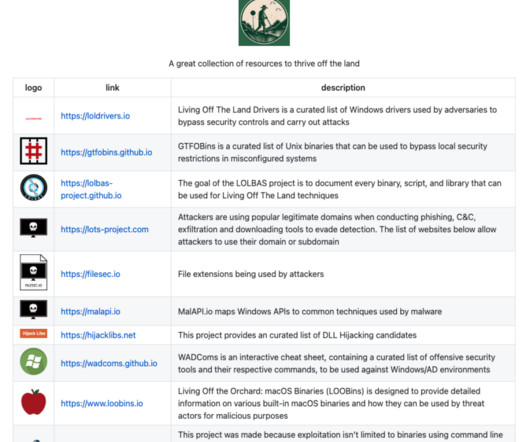
An overview of Living Off the Land (LOTL) attack techniques
Lacework
MARCH 6, 2024
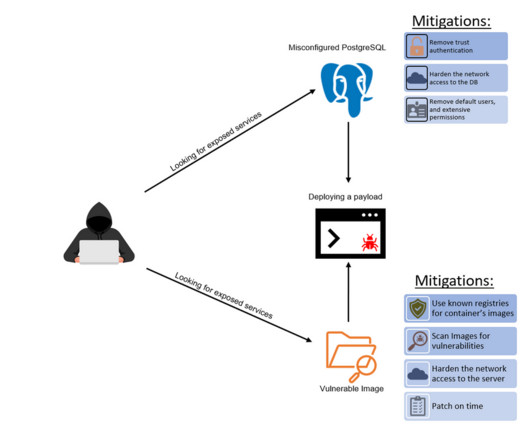
To protect critical systems and data, security teams must grasp the nuances of LOTL methods being actively utilized by attackers. This project focuses specifically on cataloging Microsoft-signed binaries that can be exploited for malicious purposes on Windows systems. The overall concept remains the same (i.e.,






































Let's personalize your content