How IT Device Discovery Can Identify Your Network's Assets and Vulnerabilities
Ivanti
JUNE 22, 2023
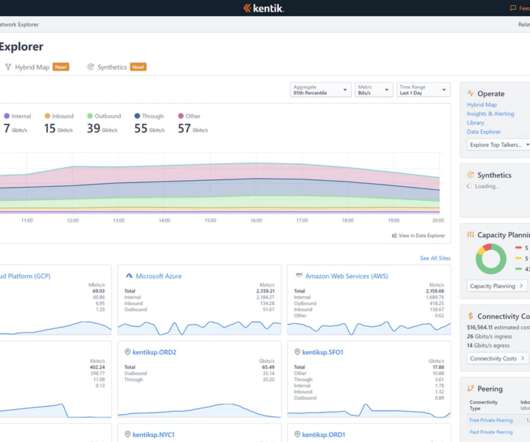
The security of your organization’s network is paramount to its success. With the ever-changing landscape of cyber threats, it's important to take the necessary steps to ensure that your network is secure and compliant with industry regulations. Ensuring compliance requires you to know what’s on your network.


















Let's personalize your content