What you need to know about Okta’s security breach
CIO
OCTOBER 25, 2023
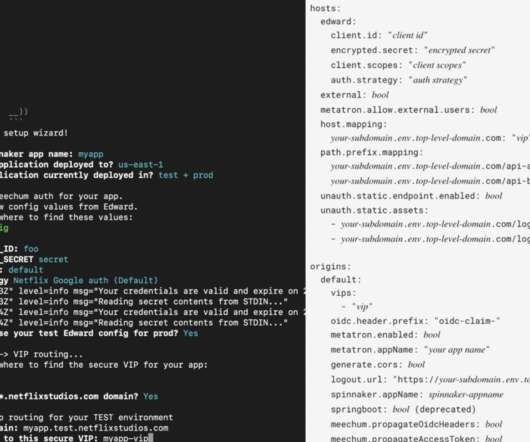
Using posture control, organizations can limit access to applications on managed devices only. Access will be prohibited if the adversaries try to access the critical applications or servers from unmanaged devices. In reaction to the attack, Okta support asked customers to upload an HTTP Archive (HAR) file to help troubleshoot issues.
















































Let's personalize your content