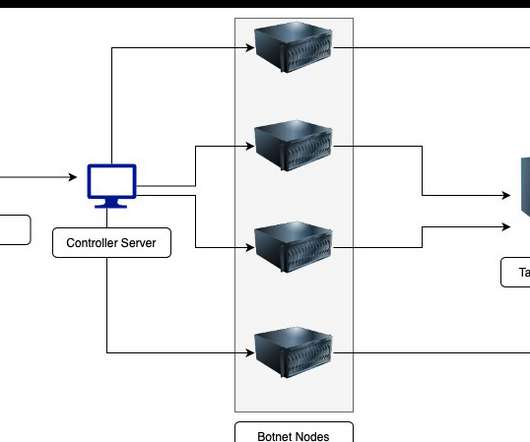
CN-Series Firewalls: Comprehensive Network Security for Kubernetes
Palo Alto Networks
JULY 28, 2020
Last week’s general availability of the Palo Alto Networks CN-Series container firewall answers these concerns, based on a deep understanding of customer challenges with Kubernetes. . Containers can simplify development as they enable DevOps teams to move fast, deploy software efficiently and save compute resources.
































Let's personalize your content