TechCrunch+ roundup: Technical due diligence, web3’s promise, how to hire well
TechCrunch
OCTOBER 25, 2022
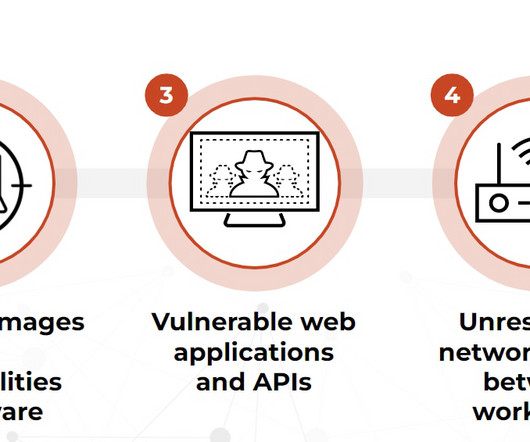
. “Whenever possible, it is far better to slowly integrate a great candidate in as an adviser or part-time contractor and let things play out,” writes Suthipongchai. 8 questions to answer before your startup faces technical due diligence. Tomorrow, we’ll run his detailed TDD checklist.














































Let's personalize your content