Why you must extend Zero Trust to public cloud workloads
CIO
NOVEMBER 8, 2023
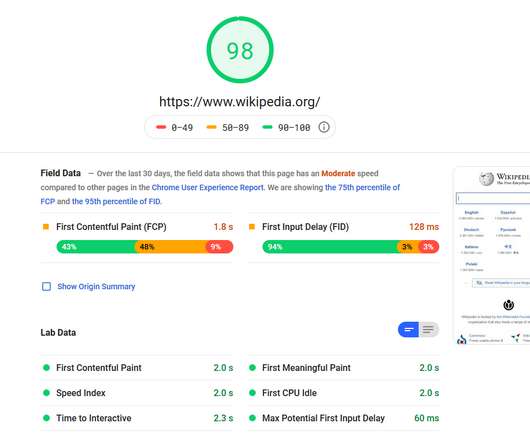
1 The rapid migration to the public cloud comes with numerous benefits, such as scalability, cost-efficiency, and enhanced collaboration. Hence, it’s important to protect the cloud and its various connections across various cloud environments, not just those that directly tie back to the on-premise network. 8 Complexity.





































Let's personalize your content