Patch Management Policy Features, Benefits and Best Practices
Kaseya
FEBRUARY 22, 2022
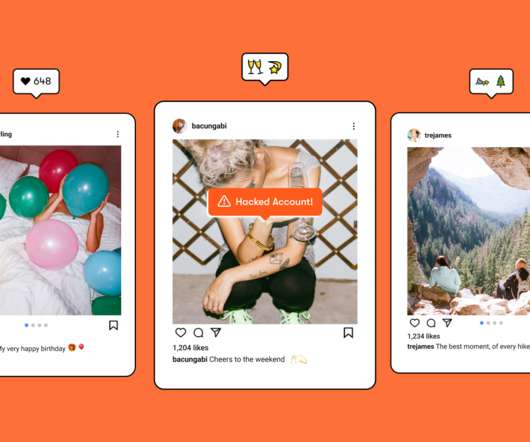
In mid-2021, cybercriminals exploited an old, unpatched memory corruption vulnerability in Microsoft Office that allowed them to remotely execute code on vulnerable devices. The above-mentioned cases illustrate the importance of patching software vulnerabilities immediately, especially those that have already been compromised.














































Let's personalize your content