Introducing Cloud NGFW for Azure — On-Prem to Azure, Seamlessly Secure
Palo Alto Networks
MAY 2, 2023
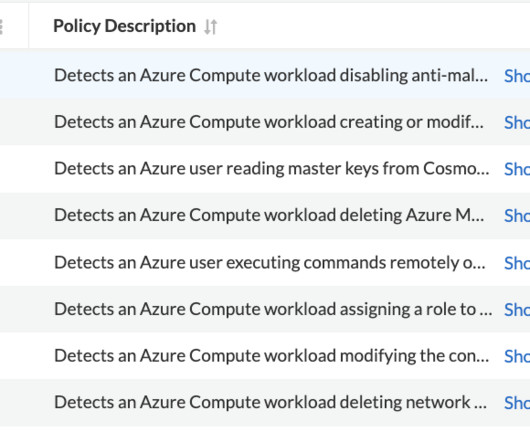
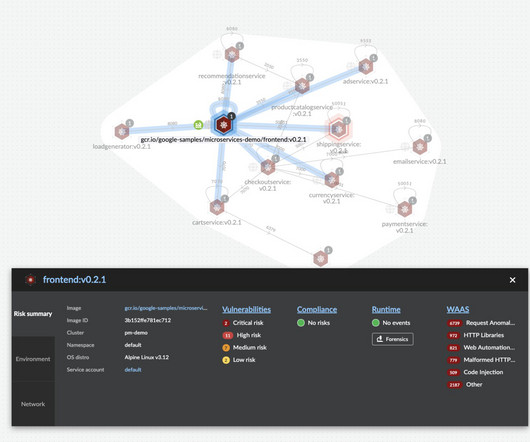
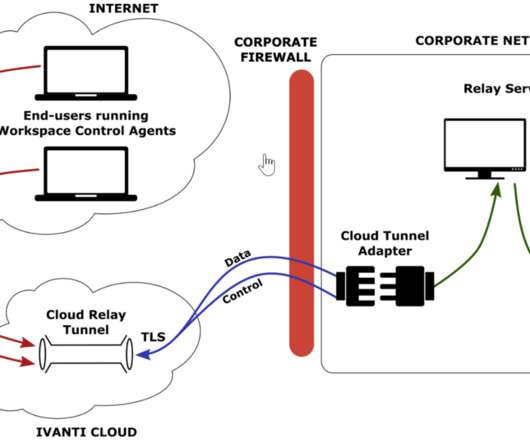
That’s why we are excited to launch Cloud NGFW for Azure to strengthen security for applications running on Microsoft Azure while streamlining network security operations. The added strength of Panorama integration makes Cloud NGFW for Azure even more powerful.













































Let's personalize your content