Backups | Roadmap to Securing Your Infrastructure
Linux Academy
MARCH 11, 2019
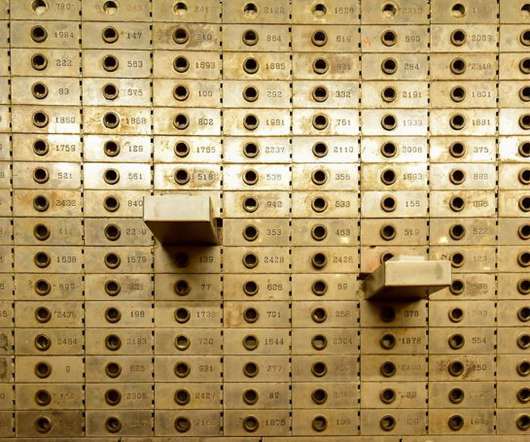
How many of you have ever needed to recover something from backups? Then, imagine if the backups of that application had been failing for months. The importance of local and cloud backups. We must plan for the worst, which includes a full system compromise and restoration from backups. Identifying backup requirements.













































Let's personalize your content