How to minimize remote access cyber security threats in 2024
CIO
JANUARY 22, 2024
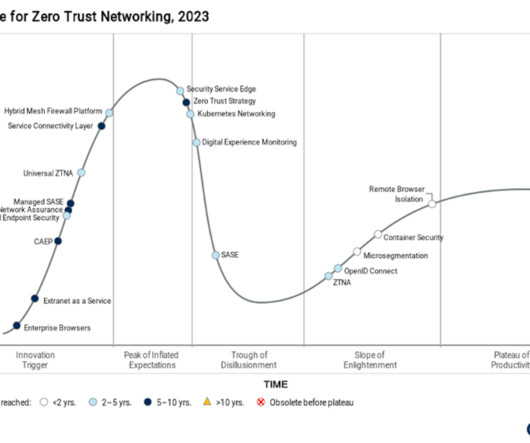
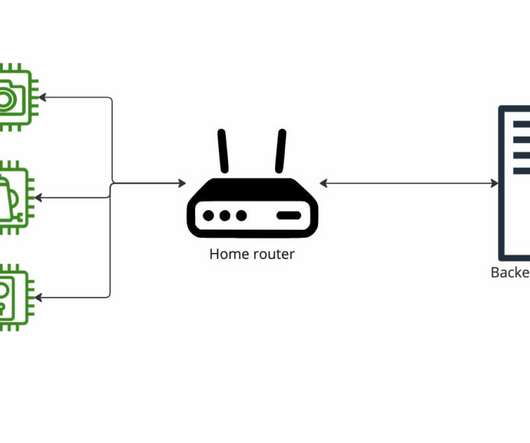
Organizations have shifted to remote desktop work environments at an increasing speed since then – simultaneously expanding their attack surface and exposing themselves to greater cybersecurity threats. However, the cloud is one increasingly popular attack surface cybercriminals have homed in on.















































Let's personalize your content