Research Shows 163% ROI with Palo Alto Networks Software Firewalls
Palo Alto Networks
DECEMBER 14, 2023
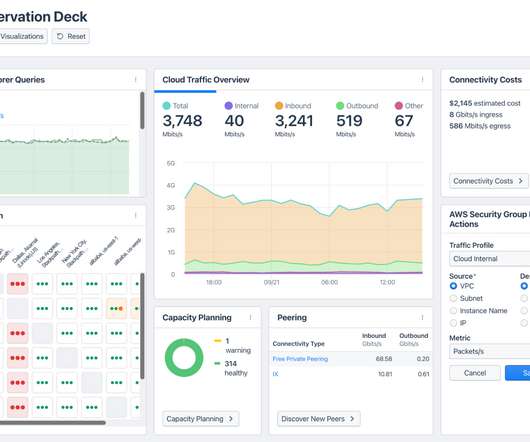
Forrester Consulting Study Now Available Good news is here for cloud and network security professionals who need proven, cost-effective solutions that substantially reduce downtime and breaches across a range of cloud and virtualized environments. Downtime due to unreliable and myriad and unreliable devices.

















































Let's personalize your content