More connected, less secure: Addressing IoT and OT threats to the enterprise
CIO
NOVEMBER 14, 2023
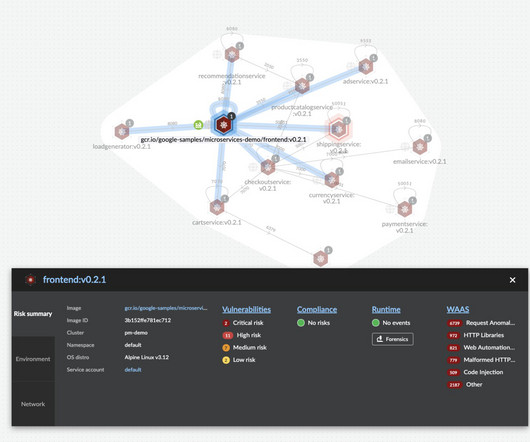
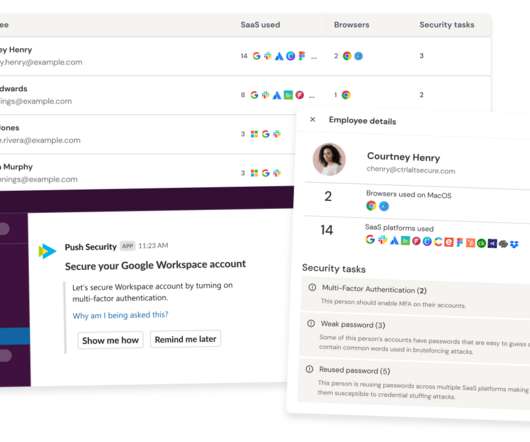
Weak authentication and authorization: One of the foremost vulnerabilities in IoT deployments stems from inadequate authentication and authorization practices. Unsanctioned devices often lack essential security controls and don’t adhere to corporate security policies. of the total number of attempted IoT malware attacks.











































Let's personalize your content