OpsMX Adds Deployment Firewall to Ensure Compliance
DevOps.com
OCTOBER 23, 2023
OpsMx announced it has added a deployment firewall to its Deploy Shield portfolio for securing CI/CD platforms.
This site uses cookies to improve your experience. By viewing our content, you are accepting the use of cookies. To help us insure we adhere to various privacy regulations, please select your country/region of residence. If you do not select a country we will assume you are from the United States. View our privacy policy and terms of use.

DevOps.com
OCTOBER 23, 2023
OpsMx announced it has added a deployment firewall to its Deploy Shield portfolio for securing CI/CD platforms.
Perficient
NOVEMBER 21, 2023
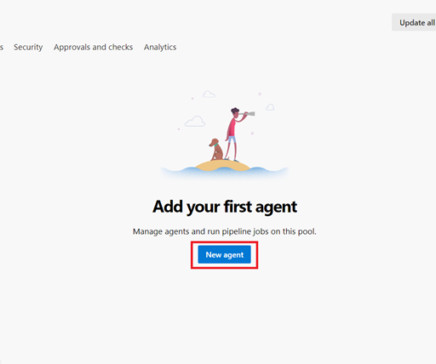
DevOps has revolutionized the software development lifecycle, emphasizing collaboration, automation, and efficiency. In the realm of DevOps, the use of build and release pipelines is essential to streamline the process of delivering high-quality software.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.

Palo Alto Networks
OCTOBER 8, 2021
Take the industry’s leading virtual firewall for a no-obligation spin in your virtualized environments. It’s never been easier, thanks to our 30-day free trial to test the VM-Series virtual firewalls for VMware ESXi and Linux KVM environments. Safeguard DevOps with security automation.

Firemon
SEPTEMBER 28, 2020
This is part 2 of a 4-part series addressing compliance myths and what you need to know about uniting compliance and security in a hybrid environment. Many organizations have adopted a passive compliance playbook. Regulations continued to change, but firewall policies may or may not have been updated. Read part #1 here.

CIO
FEBRUARY 7, 2023
Among the responses (edited slightly for clarity; this was Twitter, after all): – Lack of visibility/control over [network] activity – Complex compliance requirements compounded by lack of internal compliance expertise – Insider threats and malicious activity – and the list goes on and on @willkelly Easy to come up w/50 #cloud #infosec challenges.

CIO
JANUARY 6, 2023
DevOps engineers must be able to deploy automated applications, maintain applications, and identify the potential risks and benefits of new software and systems. The 10 most in-demand tech jobs for 2023. 25th percentile. 50th percentile. 75th percentile.

CIO
APRIL 27, 2023
There’s an ever-growing need for technical pros who can handle the rapid pace of technology, ensuring businesses keep up with industry standards, compliance regulations, and emerging or disruptive technologies. Companies can’t ignore digital transformation as technology continues to dominate nearly every aspect of business and daily-life.

Firemon
OCTOBER 26, 2021
With Halloween around the corner, here’s a real-world firewall policy horror story. ( As a Sales Engineer, I spend a lot of days doing demos of our products, talking to Security Engineers, Compliance Folks, DevOps Managers, and CISOs about firewall and network security. So it couldn’t be “snuck in”.

Firemon
OCTOBER 19, 2020
To err is human, and with many enterprises managing 100 firewalls or more, there are plenty of chances for humans to err. Almost two out of every three businesses are still using manual firewall change management processes, despite ever-increasing volumes of change requests. The costs of managing firewalls are often hidden.

OTS Solutions
APRIL 23, 2023
Cloud service providers provide ways to secure your data and information by providing firewalls to detect any unusual activity by intruders. Cloud service providers must have compliance with security standards per your needs such as HIPAA, PCI, or ISO 27000. DevOps ensures faster and better product delivery.

CIO
FEBRUARY 24, 2023
Also, there is a distinct lack of consistent understanding and standard practice for how application development should work in a modern DevOps department—such as code supply chain (open source packages and drift) or integration tools (Git, CI/CD, etc.). This creates risks. Ready to elevate the security of your development lifecycle?

CIO
NOVEMBER 14, 2023
This may include who owns the workload; its dependencies on other applications; who authored it or what vendors are involved; security, governance, compliance, and data requirements; and special integration or location requirements. Importantly, you should also indicate the goal for the workload (e.g.,

Firemon
JANUARY 3, 2019
The same goes for many of you who have to keep up with audits to maintain compliance with internal and regulatory mandates like the Payment Card Industry Data Security Standard (PCI-DSS) or the Health Information Trust Alliance (HITRUST). Click here to read how one of our customers got their compliance in shape with FireMon.

Lacework
JULY 18, 2022
For many years, the ISO 27001 certification has been an industry benchmark to show compliance with standard security practices. If you’ve never worked in compliance before, there can be the impression that achieving compliance is a simple checklist when in fact, the opposite is true. It is of course our job to protect it.

Firemon
OCTOBER 8, 2020
Manual processes around policy management slow responsiveness and lead to redundant efforts, while manual security and compliance checks across a diverse environment hinder deployment and throttle feature delivery. Some are hard to understand or are poorly written, requiring DevOps to grind out even more complex code to get them to work.

Firemon
SEPTEMBER 22, 2020
Misconfigurations are the leading cause of breaches , compliance violations, and unplanned downtime. Simplify Integration – NSPM is increasingly a part of core workflows like IT Service Management (ITSM), Security Orchestration and Automation (SOAR), as well as DevOps and CI/CD pipelines. SD-WAN, SASE, and Firewall as a Service.

Firemon
DECEMBER 2, 2020
According to the Firemon State of the Firewall 2019 report, 65 percent of organizations are using no form of automation at all to manage their network environment. Now that every company is a software company, that needs to include DevOps. Now that regulations are changing rapidly, that needs to include compliance.
Firemon
SEPTEMBER 16, 2022
The most common threat to business security is accidental firewall and cloud security group misconfigurations. The average enterprise network team is asked to make more than 100 firewall changes per week, and these changes can then take weeks to manually implement. Problem 1: Time-consuming Manual Changes.

Palo Alto Networks
JANUARY 25, 2021
Prisma Cloud Now Secures Apps with the Industry’s Only Integrated Web App Firewall (WAF), API Security, Runtime Protection and Bot Defense Platform. Detailed in a new whitepaper , our team showed that our web application firewall (WAF) capabilities outperformed six competing solutions. Host Security: Custom Compliance Policies.

Firemon
SEPTEMBER 29, 2020
Lack of visibility across all devices leads to compliance risks. Views should show data gathered from everywhere on the network, from the datacenter to the firewalls and across all environments, in real-time, and should be presented in a manner that is easy to understand so better decisions can be made faster.

Palo Alto Networks
JUNE 17, 2020
Container adoption is on a serious rise, which is why we’re releasing CN-Series , the containerized version of our ML-Powered Next-Generation Firewall (NGFW), designed specifically for Kubernetes environments. CN-Series container firewalls deployed on each node in the environment for maximum visibility and control.
d2iq
SEPTEMBER 6, 2023
features the new DKP AI Navigator, an AI assistant that enables DevOps to more easily manage Kubernetes environments. AI Navigator can help enterprise organizations overcome the Kubernetes skills gap by giving Kubernetes DevOps teams expert advice at their fingertips. D2iQ Kubernetes Platform (DKP) 2.6
Firemon
FEBRUARY 27, 2020
In the meantime, relationships with DevOps/Application team s are getting worse, with 45.4 Worse still, it’s leading to misconfigurations and incorrect setup that places organization s at a greater risk for data breaches and compliance failures. . Lack of automation raises the likel ihood of misconfigurations .

Palo Alto Networks
MARCH 25, 2020
This release offers DevOps and SecOps teams added visibility and security with advanced “shift left” capabilities and central CI/CD policy management, along with several other host security features and architecture improvements. Additional plugins, including GitLab and BitBucket, will become available soon. . Gartner Research Firm.

Perficient
MARCH 21, 2023
Meanwhile, network engineers need to ensure that the servers have valid IP addresses and that the firewalls on both sides of the DMZ are allowing the correct traffic though so that users can get to the app, and the web server can talk to the database.

Blue Sentry
DECEMBER 27, 2023
Blue Sentry Cloud Tech Talk: Why You Should Use AWS Systems Manager Hi, I’m Fabrizio Mariani, and I work here at Blue Sentry Cloud as a DevOps Team Leader. Session manager provides secure and auditable instance management without requiring to open inbound ports in firewalls, maintain Bastion hosts, or manage SSH keys.

Lacework
MAY 5, 2022
The 1990s also saw the rise of firewalls and antivirus programs, as organizations (and individuals) began storing and sharing more personal information online. Compliance issues — When sensitive data is stored in the cloud, it becomes subject to more data protection regulations. Secure Endpoints. Access Management.

Firemon
MARCH 22, 2021
The threat landscape has shifted, cloud adoption has accelerated, DevOps is more important than ever, and enterprises that once had 50 or 100 field offices now have thousands of micro-offices located in employees’ living rooms. Enterprises are already using elements of SASE, such as Firewall as a Service (FWaaS), CASB and IPS.

Lacework
SEPTEMBER 28, 2022
DevOps : While the continuous deployment of code in a cloud environment can speed development, it can also increase your attack surface. Ephemeral workloads : It’s typical to maximize resources by recycling data, firewalls, IP addresses, and drives. These workloads, and the cloud environments they’re in, change rapidly.

Perficient
JANUARY 27, 2023
These tools help build security into the entire development lifecycle and eliminate the silos between DevOps and security. Enabling compliance with security and regulatory standards by supplying visibility into the security of software systems and ensuring that they meet relevant requirements.

Blue Sentry
AUGUST 17, 2021
Managed Services typically cover things like infrastructure management, security services, DevOps, and NOC (Network Operations Center) services. Compliance checks. Compliance Checks. With all of the industry standards and regulations, compliance has truly become a full-time business. Blue Sentry Cloud.

Firemon
MARCH 31, 2021
Automating network security policy management is proven to deliver quantifiable results, such as a 400% faster policy review time and an 80% reduction in firewall and cloud security group misconfigurations. Access to a broad and deep range of integrations will enable DevOps to use its own toolchain instead of multiple proprietary SDKs.

Palo Alto Networks
APRIL 28, 2020
You can find the details in our launch blog, “ Prisma Cloud Native Security Platform Embeds Security into DevOps Lifecycle.” Compute Security is one of the four key pillars that comprise our CNSP, along with Visibility, Compliance and Governance , Network Protection and Identity Security. . Improving Host Security with AMI Scanning .

Mentormate
MAY 20, 2021
In that article about firewalls, he defined bastion hosts as “a system identified by the firewall administrator as a critical strong point in the network security. At MentorMate, we help our clients achieve the high security and compliance requirements. Learn more about our Cloud & DevOps practice.

Firemon
JULY 16, 2019
For example, automation of firewall configuration updates is very straightforward but not so much the access control rules that govern who and what should have access to which network resources. Automation and Compliance – Will the Twain Meet? Security decisions are very contextual. Automating Mindfully.

Palo Alto Networks
DECEMBER 3, 2019
Palo Alto Networks today at AWS re:Invent 2019 said it intends to integrate VM-Series virtual firewalls and Prisma Cloud, the industry’s most complete Cloud Native Security Platform (CNSP), with AWS Outposts, a new service from Amazon Web Services, In c. These capabilities will be extended to environments that leverage AWS Outposts.

Firemon
MARCH 11, 2020
It could be DevOps adding a development server, marketing people adopting a Software-as-a-Service (SaaS) CRM tool, or the business absorbing a whole host of endpoints, networks, and applications by acquiring another company. . Building assets bl ock visibility . The integration with these common tools was just the beginning.

CircleCI
MARCH 22, 2021
x, which is now available to all CircleCI customers, was designed to meet the strictest security, compliance, and regulatory restraints. For others, this means doubling down behind the firewall. Offering an exceptional on-premise service means keeping that service up-to-date with the latest releases. Enterprise-level security.

Altexsoft
JULY 2, 2020
Attempting to operate Kubernetes in production with a traditional team rather than a DevOps one, or transitioning to DevOps to use Kubernetes are ill advised. Hardening and compliance. Benchmarks can also help ensure you meet compliance with your deployment, providing proof of audits and measures taken. Kubernetes skills.

Palo Alto Networks
SEPTEMBER 8, 2021
Developers and DevOps Teams Can Now Use Prisma Cloud’s Advanced Machine Learning to Prevent Dynamic Threats Before They are Deployed Into Operational Environments. Today’s high speed deployments in a DevOps world rely on the efficient reuse of image libraries and the increasing usage of container images.

Altexsoft
OCTOBER 24, 2022
CloudOps is a methodology that takes DevOps to the cloud. CloudOps codifies best practices and procedures for cloud-based operational processes, similarly to how DevOps codifies software development and delivery processes. CloudOps vs. DevOps. Both CloudOps and DevOps are agile development methodologies.

Openxcell
OCTOBER 2, 2023
To facilitate team collaboration, IT consultants use DevOps to automate critical business processes and technical workflows. They also ensure that cloud solutions are security and compliance-compliant. Security solutions they help implement include firewalls, intrusion detection systems, and threat intelligence.

Palo Alto Networks
MARCH 6, 2020
This is basically where the idea of DevOps comes from. DevOps is an organizational mindset, established to bridge the gap between two teams: software development and IT operations. Organizations need a new methodology, that, like DevOps, will bridge teams, improve communication and automate processes. Let’s Work Together.

Planbox
APRIL 15, 2020
This scheme tested Planbox’s IT defences against the following five critical technical security controls, all of which must be met in order to achieve the Cyber Essentials accreditation: Firewalls. Secure Configuration. User Access Control. Malware Protection. Patch Management.
Expert insights. Personalized for you.
Are you sure you want to cancel your subscriptions?


Let's personalize your content