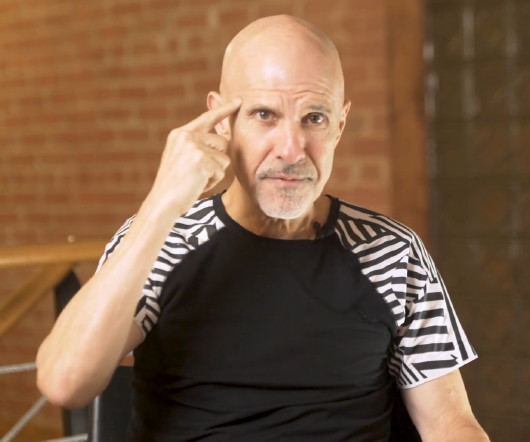
6 Negotiation Techniques You Should Add to Your Playbook
thoughtLEADERS, LLC
MAY 19, 2021
Your negotiation strategy can make or break a deal. Learning negotiation tactics is key to becoming a more strategic negotiator. Over the years, I’ve learned some great negotiating techniques and tactics. I’d like to share them now. The Invisible Man The first is called The Invisible Man. You can use this technique when you’re in the heat of a deal and you don’t want to give an answer right now, or you don’t like the position that the other party is taking.

































Let's personalize your content