Four questions for a casino InfoSec director
CIO
SEPTEMBER 21, 2023
As learned from recent cyberattacks, user education has become a critical component to protecting against these threats as well.
This site uses cookies to improve your experience. By viewing our content, you are accepting the use of cookies. To help us insure we adhere to various privacy regulations, please select your country/region of residence. If you do not select a country we will assume you are from the United States. View our privacy policy and terms of use.

CIO
SEPTEMBER 21, 2023
As learned from recent cyberattacks, user education has become a critical component to protecting against these threats as well.

Kaseya
MAY 18, 2020
As per the survey, MSPs earned an average of 30 percent of their revenue from providing traditional managed services, while other service revenues, such as professional services, backup and disaster recovery services or cloud services, lag among MSPs. Backup and Disaster Recovery Services. Whatever the reason may be?—whether
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.

TechCrunch
NOVEMBER 16, 2022
” As a company’s IT environment expands, so does the amount of passwords, API keys and certificates that the company uses to enable authentication between processes, services and databases, he notes. The core problem Akeyless attempts to tackle is what Hareven refers to as “secret sprawl.” billion by 2025.

Openxcell
NOVEMBER 28, 2023
To prevent such security threats, various enterprise application security best practices are employed, including the use of stringent authentication methods and access controls in order to prevent unauthorized access. Make sure disaster recovery plans are tested periodically to ensure that data can be recovered quickly.

Kaseya
DECEMBER 9, 2020
This could include CCTV monitoring, fire alert, on-site guards and identity authentication. Many colocation centers provide maintenance, monitoring, reporting and troubleshooting to help prevent potential disasters like system failures, security breaches and outages. Disaster Recovery Preparedness. Uptime SLAs.

Cloudera
DECEMBER 16, 2020
Replication is one of HBase’s most popular capabilities as it provides an automatic disaster-recovery (DR) solution, supports data migration, supports workload partitioning and/or supports a search-based secondary index through integration with Apache Solr. Replication from insecure to secure clusters. Conclusion.

Kaseya
MAY 13, 2021
A cloud service provider generally establishes public cloud platforms, manages private cloud platforms and/or offers on-demand cloud computing services such as: Infrastructure-as-a-Service (IaaS) Software-as-a-Service (SaaS) Platform-as-a-Service (PaaS) Disaster Recovery-as-a-Service (DRaaS). Compliance, Security and Disaster Recovery.

CTOvision
FEBRUARY 22, 2017
Such plans may include senior management buy-in, maintaining digital asset inventories, implementing ACLs and monitoring of physical and IT infrastructure, testing a disaster recovery plan, and investing in employee security training.

Kaseya
JUNE 24, 2019
Implement multi-factor authentication (MFA). Multi-factor authentication adds an extra layer of security to the login procedure beyond using just a password. The most common form of MFA is two-factor authentication (2FA). It has an authenticator app for iPhone and Android devices. Detect and respond to insider threats.

Perficient
MAY 18, 2023
for new initiatives/changes & operational excellence to run the business as usual Business Continuity and Disaster Recovery considerations The list can go on and on… Only those who have an agile and the right mindset can adapt, survive, and thrive.

Aviatrix
AUGUST 11, 2018
Dennis : We focus more on business continuity as opposed to DR (disaster recovery) which is more reactive. It would be great if you can integrate with Google authenticator for your 2FA. We’ll look into Google authenticator. Sherry : How do you operate differently now that you are 90% in AWS? Sherry : Thank you.

InfoBest
MARCH 23, 2020
Use a multi-factor authentication and Data-at-Rest Encryption to a perimeter and internal firewall to ensure the safety of your data. Adequate data backup measures and disaster recovery are necessary. Two significant factors that keep the system regulated and safe from harm are authentication and encryption.

Tenable
JUNE 23, 2023
Here’s what it recommend: Be as prepared as possible for a ransomware attack, including having data backups; a business continuity and disaster recovery plan for critical applications; cyber insurance coverage; and updated threat intelligence information.
Tenable
AUGUST 9, 2022
All three vulnerabilities require authentication and user interaction to exploit — an attacker would need to entice a target to visit a specially crafted Exchange server, likely through phishing. 31 Elevation of Privilege Vulnerabilities in Azure Site Recovery. This certificate would allow the attacker to elevate their privileges.
Progress
DECEMBER 30, 2019
But for external auth providers, it is just not worth the risk to an organization so developers prefer commercial providers such as those available with Kinvey to authenticate against identity systems such as SAML, OAuth2, OpenID, Active Directory and LDAP. href ); promise.then(function onSuccess( user ) {.
Progress
DECEMBER 30, 2019
But for external auth providers, it is just not worth the risk to an organization so developers prefer commercial providers such as those available with Kinvey to authenticate against identity systems such as SAML, OAuth2, OpenID, Active Directory and LDAP. href ); promise.then(function onSuccess( user ) {.

CIO
FEBRUARY 1, 2024
In addition, what are the costs associated with incorporating the new software into the organization’s security infrastructure in areas such as access control, authentication, and zero trust. Organizations keep multiple copies of application data for backup and disaster recovery reasons, so companies need to add the cost of replacing backups.
O'Reilly Media - Ideas
DECEMBER 6, 2022
Cyberattacks are increasingly targeted at small to medium businesses , the vast majority of which don’t have plans for defense or disaster recovery. Multifactor Fatigue is a new kind of attack against multifactor authentication: bombarding a user with automation requests, hoping that they will accidentally approve one.

Openxcell
OCTOBER 20, 2023
c) What is the disaster recovery plan? i) What are the authentication methods they facilitate? d) What measures do they have to protect various access components? e) What technical support are they ready to provide? f) What are the results of the most recent penetration test? g) Do the providers encrypt the data?

Capgemini
AUGUST 27, 2020
Leaders must inspire their workforce to innovate and create change through encouraging ownership, trusting their teams, and displaying ethical, authentic, and cooperative behavior. We ran disaster recovery testing exercises or “game days” in order to build strong bonds and trust in cross collaborating teams.

CIO
OCTOBER 4, 2023
Critical documents such as statements, bills, invoices, or verification letters should include electronic seals, or e-seals, that virtually demonstrate authenticity and integrity of the document as well as verify the identity of the document’s origin. Provide access control.

Kaseya
DECEMBER 7, 2021
Furthermore, you can reduce downtime with instant recovery, ransomware detection and automated disaster recovery testing by leveraging the Kaseya Unified Backup integration in VSA.

Actian
MARCH 13, 2019
Major incident management and disaster recovery for cloud-based applications is much easier, because remote operators can quickly and easily re-deploy applications to a new location from an administrative console. Further, authentication, authorization, logging, and auditing are also built into all cloud platforms.

CIO
DECEMBER 7, 2023
Passwordless authentication A modern PAM cybersecurity solution must support several existing passwordless methods such as PKI, SSH keys and certs, and FIDO2 dongles. Building authentication services and MFA into the PAM platform (see above) enables rapid innovation and support for newer standards such as Passkeys.

Datavail
OCTOBER 3, 2022
AWS offers a variety of options for backing up and restoring your systems, including AWS Backup and CloudEndure Disaster Recovery. Any new resources added to an environment should not be able to interact with anything until they are authenticated and authorized to ensure that they are legitimate.

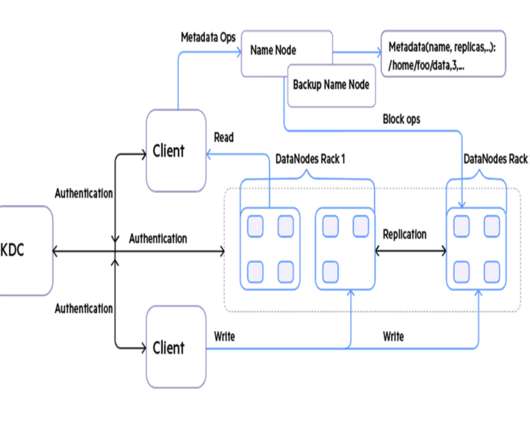
Cloudera
SEPTEMBER 1, 2020
HDFS also provides snapshotting, inter-cluster replication, and disaster recovery. . It intercepts REST/HTTP calls and provides authentication, authorization, audit, URL rewriting, web vulnerability removal and other security services through a series of extensible interceptor pipelines.

Kaseya
FEBRUARY 4, 2021
Many companies use weak encryption and very basic authentication login methods, which can be dangerous for login security. . Backup and Disaster Recovery . Two-Factor Authentication . Subsequently, Zoom took steps to improve the security of their software over the past year. . How Does Your Solution Stack Up?
Perficient
MARCH 27, 2023
multi-factor authentication, single sign-on, security policies, user and device management. Backup & Disaster Recovery: Proactive strategies for backup and disaster recovery to minimize impact of potential outages, protect your data and restore your environments to maintain business continuity.

OTS Solutions
APRIL 23, 2023
What are their security measures and disaster recovery options? Disaster Recovery options: Cloud services come with the best disaster recovery options. Since it helps in authenticating the user’s identity. Then you must understand their answers and if they are best for you.

Strategy Driven
MAY 20, 2021
They can use external data centers to track all your essential data and launch a backup disaster recovery if your system crashes. A two-factor authentication code further protects them. Tech support can provide you with more options to retrieve your data outside of cloud computing. Firewall Services.
Xebia
MARCH 28, 2024
API Security at the application level Cloud services have introduced convenient ways to secure which traffic can access certain information, but relying on network layer controls to authenticate and authorize who can access your data can leave you open to bypassed controls. In some scenarios, this may be the only option.

CIO
JUNE 20, 2023
The two data centers have been put in place to manage disaster recovery, the company said. “Oracle EU Sovereign Cloud gives customers the services and capabilities of Oracle Cloud Infrastructure’s (OCI) public cloud regions with the same support, and service level agreements (SLAs) to run all workloads,” Oracle said in a statement.

CTOvision
JUNE 3, 2014
Later, more and more security related capabilities were added, including better access control, authentication, auditing, and data provenance. In the early days of production systems built around Apache Hadoop, security was only possible by limiting access to your cluster.

Kaseya
NOVEMBER 29, 2022
To ensure business continuity and data security, businesses must implement a layered cybersecurity framework that includes both RMM (remote monitoring and management) and BCDR (business continuity and disaster recovery) solutions. What can you do to avoid damage? Benefits of VSA and Datto BCDR integration.

Kaseya
NOVEMBER 9, 2020
Backup and Disaster Recovery. If you are an IT professional, you know how important it is to backup your critical systems so that data can be recovered in the event of a system failure due to a natural disaster, bad update, malicious cyberattack or other issues. Two-Factor Authentication (2FA). Conclusion.

Datavail
FEBRUARY 2, 2021
One reason for its widespread adoption is the powerful security and disaster recovery capabilities it has available. Workloads in MariaDB can be protected with many options, from encryption to user authentication. LDAP Authentication: Meet your enterprise-grade database requirements with LDAP support. Read This Next.

CloudGeometry
APRIL 25, 2022
6 Business Continuity and Disaster Recovery While technology options to avoid downtime continue to improve, downtime is still costly. It does not matter to them whether this results from a malicious hack, natural disaster, or even an outage due to a hardware failure or human error. Read more here. #6

Kaseya
FEBRUARY 11, 2021
Your IT Valentine also makes use of two-factor authentication (2FA) to enhance login security. Reliable Backup and Disaster Recovery. Your IT Valentine integrates with various backup and disaster recovery (BDR) solutions for IT systems and SaaS applications, allowing you to recover quickly from an attack.

OTS Solutions
DECEMBER 4, 2023
Security Layer Finally, the security layer ensures the protection of data and resources through authentication, encryption, and other security measures. Can private cloud architecture be used for disaster recovery? Ans) Private cloud architecture can indeed be utilized for disaster recovery purposes.

OTS Solutions
FEBRUARY 16, 2023
It results in better disaster recovery. You also need to ensure the authorization and authentication security level. It gives better user accessibility and reduces operational costs. Do not ignore user feedback and experience to ensure the performance of the system. 8.

Kaseya
SEPTEMBER 24, 2019
Back up and disaster recovery (BDR) has become an important security process for small and large businesses alike. This includes multi-factor authentication (MFA) to protect access to their RMM. Leverage Multi-factor Authentication (MFA) to Secure Backup . Request a demo of Kaseya Unified Backup here. . .

Kaseya
NOVEMBER 9, 2023
Business continuity and disaster recovery (BCDR): Cloud computing serves as a robust foundation for business continuity and disaster recovery strategies for organizations. This eliminates the risk of data loss and provides a reliable mechanism for long-term data retention.
Progress
DECEMBER 30, 2019
But for external auth providers, it is just not worth the risk to an organization so developers prefer commercial providers such as those available with Kinvey to authenticate against identity systems such as SAML, OAuth2, OpenID, Active Directory and LDAP. href ); promise.then(function onSuccess( user ) {.

Perficient
MARCH 29, 2023
As expected, this led to a growth of shadow IT among the more sophisticated user base, who needed more advanced functionality but were less able to manage licensing, security and disaster recovery than the formal IT offering. We ended up installing a hybrid Elastic Cloud Enterprise solution.
Expert insights. Personalized for you.
Are you sure you want to cancel your subscriptions?


Let's personalize your content