How Watchdog smuggles malware into your network as uninteresting photos
Lacework
JULY 15, 2022
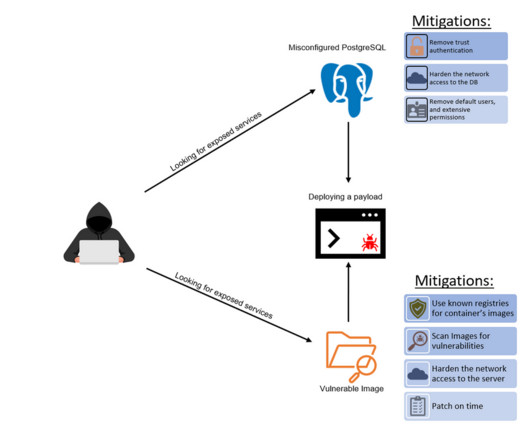
This ancient technique has found its place in the world of malware, namely hiding malicious code within other files including image formatted files ( T1027.003 ). This blog takes a look at the latter technique in recent cryptojacking activity from a group known as WatchDog. Steg malware is uncommon relative to other malware.















































Let's personalize your content