Russian Cyberspies Deliver ‘GooseEgg’ Malware to Government Organizations
Ooda Loop
APRIL 23, 2024
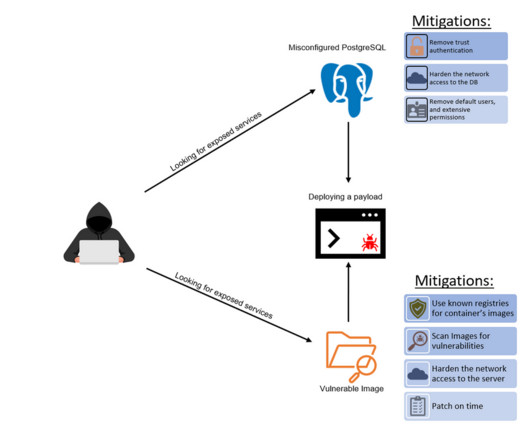
According to a Microsoft report, Russian-linked cybercrime group APT28 has been exploiting Windows Print Spooler vulnerabilities to deploy an exploitation tool against organizations across Western Europe, in Ukraine, and in the US.











































Let's personalize your content