11 Tips to Keep Your Company’s IT Systems Safe
Invid Group
SEPTEMBER 29, 2023
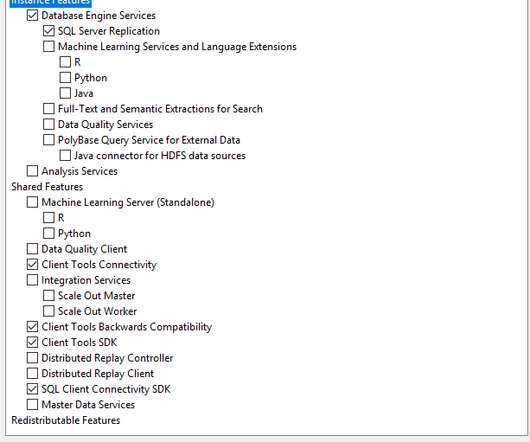
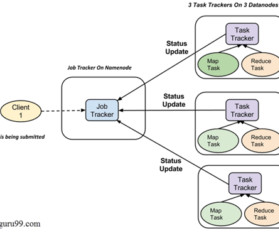
11 Tips to Keep Your Company’s IT Systems Safe BY: INVID In today’s digital age, businesses rely heavily on IT systems to operate efficiently. This involves identifying vulnerabilities and potential weaknesses in your systems. In-house IT teams or external experts can perform security audits.


















































Let's personalize your content