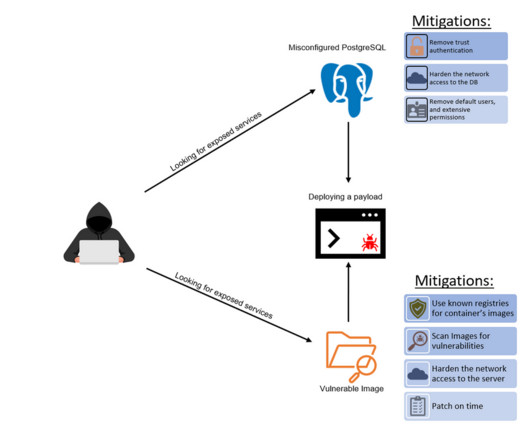
Kinsing Malware Hides Itself as a Manual Page and Targets Cloud Servers
Tenable
MAY 16, 2024
One of the most common cryptomining threats for cloud environments is the Kinsing malware. Kinsing is a notorious malware family active for several years, primarily targeting Linux-based cloud infrastructure. The Kinsing malware uses different locations to stay undetected and hides itself as a system file.
















































Let's personalize your content